Navigating GDPR, HIPAA, and Other Consent Standards
Post Summary
Patient consent is a cornerstone of privacy in healthcare, but meeting the requirements of laws like GDPR, HIPAA, and others can be challenging. Here's a quick breakdown:
- HIPAA (U.S.): Allows sharing of health data for treatment, payment, and operations without explicit consent but requires formal authorization for marketing, selling data, or other non-standard uses.
- GDPR (EU): Requires explicit consent for processing sensitive health data, with strict rules on withdrawal, documentation, and breach notifications within 72 hours. These requirements are critical as data breaches can severely disrupt clinical operations.
- Other Frameworks: Laws like CCPA (California), PIPEDA (Canada), and LGPD (Brazil) add unique consent rules, such as opt-out models or mandatory data protection officers.
Key differences include consent triggers, breach reporting timelines, and data retention rules. Organizations should aim to follow the most stringent requirements, such as GDPR's explicit consent and documentation standards, to ensure compliance across jurisdictions.
Quick Comparison:
| Feature | HIPAA (U.S.) | GDPR (EU) | CCPA (California) | PIPEDA (Canada) | LGPD (Brazil) |
|---|---|---|---|---|---|
| Consent for Health Data | Not always required | Explicit consent | Opt-out model | Opt-in (some cases) | Opt-in |
| Breach Notification | 60 days | 72 hours | Without delay | Real harm threshold | Reasonable time |
| Right to Erasure | No general right | Yes (Article 17) | Limited | Limited | Yes |
| Max Penalty | $1.9M annually | €20M or 4% revenue | $7,500 per issue | CAD 100K per issue | 2% revenue (BRL 50M) |
To simplify compliance, use automated consent management tools, maintain clear records, and follow GDPR-level standards wherever possible.
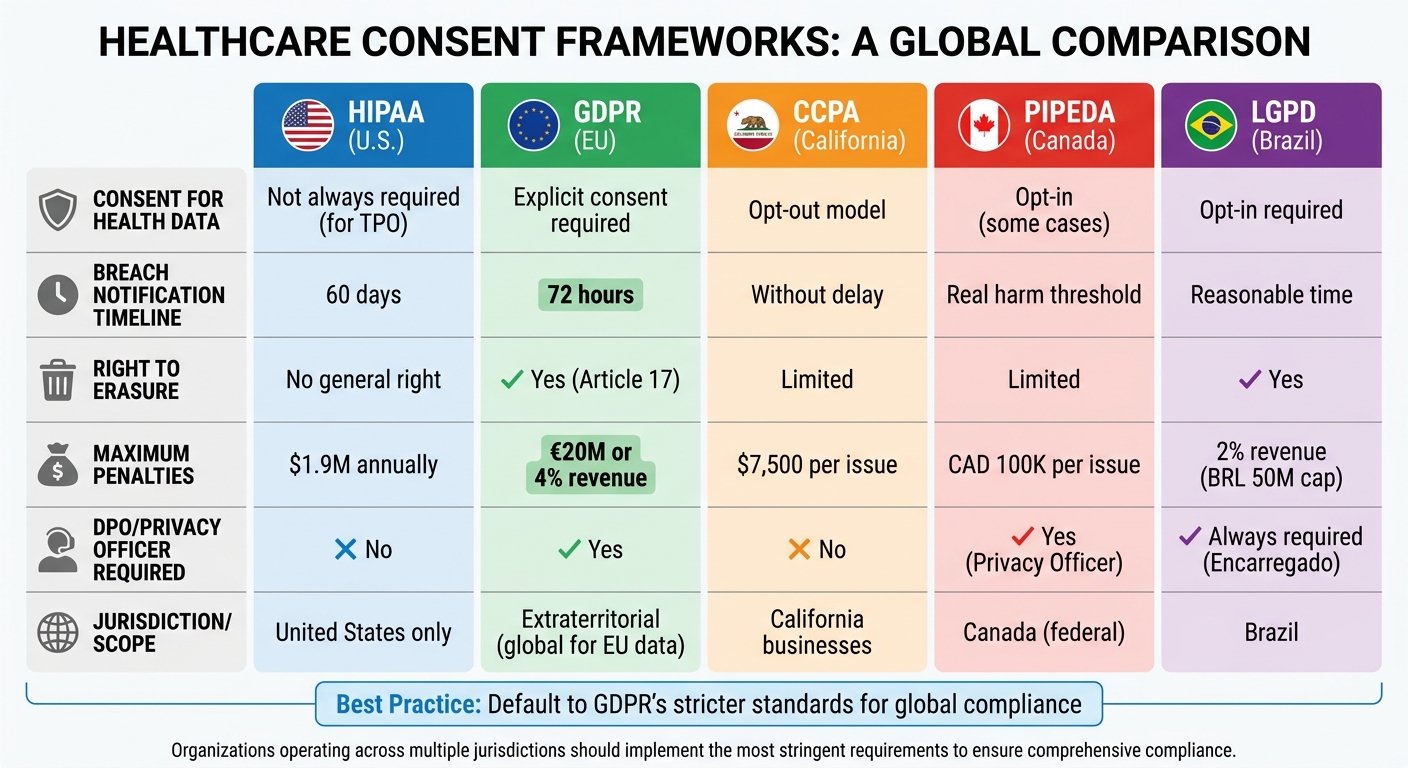
GDPR vs HIPAA vs CCPA vs PIPEDA vs LGPD Healthcare Consent Requirements Comparison
HIPAA Consent Requirements
When HIPAA Requires Patient Consent
HIPAA sets clear boundaries between routine TPO (Treatment, Payment, and Healthcare Operations) disclosures and situations that demand formal patient authorization. This distinction helps healthcare providers determine when they need explicit patient approval before sharing Protected Health Information (PHI).
For routine activities like coordinating treatment, processing payments, or managing internal operations, HIPAA does not require patient consent. For instance, doctors can consult with specialists, hospitals can bill insurance companies, and organizations can conduct quality assessments without needing written permission. These activities fall under the TPO category, which allows for smoother healthcare operations.
However, there are specific scenarios where patient authorization is mandatory. These include:
- Marketing efforts involving compensation
- Selling PHI
- Sharing psychotherapy notes
- Disclosures related to employment
- Insurance underwriting
- Publicly posting identifiable patient details
- Research not approved by an Institutional Review Board (IRB)
- Sharing information with non-care-related parties
"Where the Privacy Rule requires patient authorization, voluntary consent is not sufficient to permit a use or disclosure of protected health information unless it also satisfies the requirements of a valid authorization." - U.S. Department of Health and Human Services [4]
Healthcare providers must first determine whether a request for PHI falls under TPO. If it doesn’t, a specific HIPAA-compliant authorization form signed by the patient is required. This distinction is critical for ensuring compliance with HIPAA regulations.
Requirements for HIPAA-Compliant Consent
When authorization is required, it’s not enough to simply gather a patient’s signature. A valid HIPAA authorization form must include several key elements:
- A detailed description of the PHI to be shared
- The name of the person or entity authorized to disclose the information
- The name of the recipient receiving the PHI
- A clear explanation of the purpose for sharing the information
- An expiration date or event (e.g., "end of research study")
- The patient’s signature and the date
- Instructions on how the patient can revoke the authorization in writing
- A statement clarifying whether treatment or payment depends on signing the form
- A notice that once disclosed to a third party, the PHI may no longer be protected under HIPAA and could be re-disclosed
The form must be written in plain, easy-to-understand language, avoiding medical jargon or complicated legal terms. Additionally, it should include clear contact details for patients who wish to revoke their authorization.
Healthcare organizations are required to keep signed authorization forms for at least six years from the date they were created or last effective [2]. This documentation is a critical component when you conduct effective third-party risk assessments to ensure vendor compliance. Patients also have the right to revoke their authorization at any time in writing. However, this revocation does not apply to actions already taken based on the original authorization. Violations of HIPAA can result in steep penalties, ranging from $100 to $50,000 per violation, with an annual cap of $1.5 million for a single category of violations [3].
Even with proper authorization, healthcare providers must adhere to the "minimum necessary" standard. This means only sharing the amount of PHI needed to fulfill the stated purpose, ensuring patient privacy remains a priority while allowing necessary information sharing.
sbb-itb-535baee
GDPR Consent Standards for Health Data
GDPR Consent Principles
Under Article 9 of the General Data Protection Regulation (GDPR), health data is categorized as "special category" data, meaning it requires stricter protections compared to standard personal data. This includes medical records, information from wearable devices, medical devices, mental health data, and even health-related insights derived from behavior.
While consent for general data processing requires "unambiguous" agreement, processing health data demands explicit consent. This means individuals must provide a clear, deliberate statement specifically addressing the sensitive health data involved. Pre-checked boxes, silence, or general terms of service cannot be used to meet this standard.
"Explicit consent must be obtained from medical data subjects for any insider interactions that aren't related to direct patient care." - Revolve Healthcare [1]
For consent to meet GDPR standards, it must adhere to these principles:
- Freely given: Individuals must have a genuine choice without coercion.
- Specific: Separate consent must be obtained for different processing purposes.
- Informed: Individuals must know who controls their data, what is being collected, and how it will be used.
- Clear: Consent must result from an affirmative action, such as checking a box or signing a form.
- Documented: Organizations must maintain records proving consent was obtained.
- Withdrawable: Individuals must be able to revoke consent as easily as they gave it.
A notable trend is that over 80% of health apps in European app stores rely on user consent as their primary legal basis for processing health data. Enforcement actions have highlighted the importance of compliance: for example, the Swedish Data Protection Authority issued a €12 million fine in 2024, and the Italian Garante imposed a €1.5 million penalty for bundling health data consent with marketing consent [5].
To comply with GDPR, healthcare organizations are encouraged to implement two-step consent processes. This could involve an initial screen where users select specific data types for processing, followed by a confirmation screen summarizing their choices. Separating health data consent from marketing preferences and general terms of service helps meet GDPR's requirement for specificity.
This framework for obtaining consent naturally leads to the requirements for managing consent withdrawal and maintaining detailed records.
Consent Withdrawal and Record-Keeping Requirements
GDPR Article 7 builds on these consent principles by establishing clear rules for both withdrawing consent and maintaining documentation. Organizations must keep detailed records that demonstrate how and when consent was obtained, ensuring they have an audit trail ready for regulatory scrutiny.
"The data subject shall have the right to withdraw his or her consent at any time... It shall be as easy to withdraw as to give consent." - Article 7, GDPR [7][9]
The withdrawal process must be as simple as the initial consent process. For example, if a patient provided consent with a single click, they should be able to withdraw it just as easily. Once consent is withdrawn, all related data processing must stop immediately. Systems should be automated to ensure this happens, including deleting or anonymizing data and notifying any third-party processors.
Record-keeping requirements include documenting:
- The unique identifier of the individual.
- The timestamp of consent.
- The version of the consent statement provided.
- The method of capture (e.g., web form or in-person signature).
- The current consent status (granted or withdrawn).
Storing these records separately from user profiles helps ensure a reliable audit trail. While GDPR does not mandate a specific expiration date for consent, some authorities suggest refreshing consent every two years to maintain its validity [7][8]. Organizations must retain these records for as long as the data is being processed to comply with accountability standards.
Additionally, under Article 33, healthcare providers must report data breaches to supervisory authorities within 72 hours - a much shorter timeframe than the 60-day window allowed under HIPAA [1][6].
To streamline compliance, organizations can implement a consent inventory. This inventory should track details such as who consented, when and how they consented, and which privacy policy version was presented. Maintaining version control ensures that organizations can verify what information patients were given at the time of consent. This systematic approach not only supports compliance but also helps build trust with patients.
Data Privacy & Compliance: GDPR, HIPAA & Best Practices Explained
HIPAA vs. GDPR Consent Standards
This section breaks down how HIPAA and GDPR differ when it comes to consent triggers and validity criteria, highlighting the challenges for organizations navigating both frameworks.
Consent Triggers and Validity Criteria Comparison
HIPAA and GDPR approach consent very differently. Under HIPAA, disclosures for Treatment, Payment, and Healthcare Operations (TPO) don’t require patient consent. This allows healthcare providers to share Protected Health Information (PHI) with other providers, insurers, and business associates without prior patient approval, as long as the purpose aligns with TPO.
In contrast, GDPR treats health data as "special category data" under Article 9, requiring explicit consent or a specific legal justification for each processing activity involving EU users’ data. For companies handling data across jurisdictions, this poses a compliance challenge.
"If you're building a health tech product that processes EU user data, relying on HIPAA's TPO exception won't satisfy GDPR. You need a separate legal basis for each processing activity." - Custodia [10]
Here’s a quick comparison of the two frameworks:
| Feature | HIPAA | GDPR |
|---|---|---|
| Consent for Health Data | Not required for TPO | Required (explicit consent or Article 9 basis) |
| Right to Erasure | No general right to erasure | Yes (Article 17) |
| Breach Notification | 60 days | 72 hours |
| Jurisdiction | United States only | Extraterritorial (applies globally for EU data) |
| Vendor Contract | Business Associate Agreement (BAA) | Data Processing Agreement (DPA) |
| Maximum Penalties | $1.9 million annual cap per category | €20 million or 4% of global turnover |
For organizations working with both U.S. and EU patients, the safest path is to default to GDPR’s stricter requirements. For example, adhering to GDPR’s 72-hour breach notification window ensures compliance with both standards [10].
This contrast sets the stage for a deeper look at managing consent withdrawal, where the operational differences between the two frameworks become even more pronounced.
Managing Consent Withdrawal Across Frameworks
Handling consent withdrawal is tricky when balancing GDPR’s erasure rights with HIPAA’s record retention rules. GDPR’s Article 17 gives individuals the "right to be forgotten", allowing them to withdraw consent and request data deletion. HIPAA, however, doesn’t offer this right. Instead, healthcare entities must comply with state laws that often mandate retaining medical records for specific periods.
When an EU patient requests data erasure, organizations need to determine whether HIPAA or state laws require retaining the data. If retention is necessary, the organization must document the legal obligation as an exception to GDPR’s erasure rules [10]. This approach ensures compliance while maintaining transparency with the patient.
"The core strategy for managing GDPR vs HIPAA is to build to the stricter standard wherever the frameworks conflict, and to maintain clear documentation of your legal basis for each processing activity under each framework." - Custodia [10]
To simplify consent withdrawal management, organizations should implement dedicated consent workflows for EU users. These workflows allow for precise tracking of consent withdrawal, which is essential under GDPR but not typically required under HIPAA’s TPO provisions [10]. Maintaining a Record of Processing Activities (RoPA) for EU data helps ensure accountability and compliance with GDPR.
Adopting GDPR’s one-month response timeframe for withdrawal requests and its 72-hour breach notification rule can help organizations meet the stricter standards of both frameworks [10]. This careful, nuanced approach is essential for protecting patient data and staying compliant across jurisdictions.
Other Regional Consent Frameworks
Beyond GDPR and HIPAA, there are other regional frameworks that significantly influence how patient data consent is handled. Healthcare organizations must carefully navigate the varying privacy laws and consent requirements across regions, each with its own enforcement mechanisms.
CCPA, PIPEDA, and LGPD Overview
The California Consumer Privacy Act (CCPA), along with its successor, the California Privacy Rights Act (CPRA), operates on an opt-out model rather than GDPR's opt-in approach. This means businesses can collect data without explicit consent but must provide a "Do Not Sell" option for consumers to opt out of data sharing. The law applies to for-profit entities with annual revenues exceeding $25 million or those handling the personal information of 100,000 or more consumers. Notably, it also grants consumers the right to sue for data breaches, with statutory damages ranging from $100 to $750 per incident per consumer [11].
In Brazil, the Lei Geral de Proteção de Dados (LGPD) shares similarities with GDPR but includes 10 legal bases for processing data, compared to GDPR's six. For healthcare, bases like "health protection" and "protection of life" are particularly relevant. LGPD also requires data controllers to appoint a Data Protection Officer (DPO), referred to as the Encarregado, and imposes penalties of up to 2% of a company's revenue in Brazil, capped at BRL 50 million per violation [11].
Canada’s Personal Information Protection and Electronic Documents Act (PIPEDA) emphasizes obtaining meaningful consent and ensuring data is used for reasonable purposes. While it generally requires opt-in consent, it allows implied consent for non-sensitive information under specific conditions. Violations under PIPEDA can result in fines up to CAD 100,000 per incident. Proposed updates through Bill C-27 could increase penalties to 5% of global revenue or CAD 25 million. For secondary uses, such as AI model training or analytics, PIPEDA and Ontario’s PHIPA mandate renewed consent if the data's purpose changes [11][12].
Multi-Framework Compliance Challenges
The contrasting requirements of these frameworks make compliance a complex task. For instance, CCPA’s opt-out model differs sharply from GDPR’s explicit opt-in requirement, underscoring that a universal consent mechanism is impractical. Companies operating across regions like California, the EU, and Brazil must adapt their consent management systems to meet jurisdiction-specific rules.
"GDPR remains the global benchmark, and compliance with GDPR provides 70-80% coverage for most other privacy laws." – ECOSIRE Research and Development Team [11]
To manage this complexity, many organizations use GDPR as the baseline standard. This approach often involves granular consent management platforms that allow jurisdiction tagging, often integrated with automated vendor risk assessment tools, enabling opt-in mechanisms for EU and Brazilian users while maintaining opt-out options for California residents. However, it’s worth noting that HIPAA’s "Safe Harbor" de-identification standards may not meet GDPR or LGPD anonymization requirements. If re-identification is reasonably possible, the data remains classified as personal under these stricter frameworks [11][12].
| Feature | CCPA/CPRA (California) | PIPEDA (Canada) | LGPD (Brazil) |
|---|---|---|---|
| Consent Model | Opt-out | Opt-in (implied for non-sensitive data) | Opt-in |
| Legal Basis Required | No | Yes (Knowledge and consent) | Yes (10 bases) |
| DPO Requirement | No | Yes (Privacy Officer) | Always required |
| Max Penalty | $7,500 per intentional violation | CAD 100K per violation | 2% revenue / BRL 50M cap |
| Breach Notification | Without unreasonable delay | "Real risk of significant harm" threshold | "Reasonable time" |
These differences highlight the need for tailored consent workflows, adding to the already significant challenges of maintaining compliance across multiple legal frameworks.
Strategies for Multi-Framework Consent Compliance
These strategies provide practical ways to navigate multiple regulatory requirements while aligning with consent frameworks.
Common Safeguards Across Consent Frameworks
Instead of juggling separate protocols for HIPAA, GDPR, CCPA, and other frameworks, it's more efficient to adopt the strictest requirements across all frameworks as a universal standard. This simplifies processes and ensures compliance with every regulation [13].
For instance, using AES-256 encryption for data at rest and TLS 1.2 or higher for data in transit goes beyond the requirements of HIPAA, GDPR, and other regulations [13]. Similarly, access to sensitive data can be restricted through Role-Based Access Control (RBAC) and Multi-Factor Authentication (MFA). GDPR’s emphasis on data minimization also calls for regular audits and logs of data access - ideally reviewed quarterly [13].
When it comes to breach notifications, regulatory timelines differ. For example, HIPAA allows up to 60 days, while GDPR mandates notification within 72 hours. To avoid confusion, adopting GDPR’s stricter 72-hour standard ensures compliance with both frameworks [14].
| Safeguard | HIPAA Requirement | GDPR Requirement | Recommended Standard |
|---|---|---|---|
| Encryption | Required for data in transit/rest | Recommended under Article 32 | AES-256 for data at rest, TLS 1.2+ for data in transit |
| Access Controls | Limit to authorized personnel | Data minimization plus RBAC | RBAC with MFA and quarterly reviews |
| Breach Notification | Within 60 days | Within 72 hours | 72-hour notification for all parties |
| Audit Trails | Required under the Security Rule | Records of processing (Article 5) | Immutable logs with UTC timestamps |
| Consent Withdrawal | Applies to future uses only | Immediate cessation, with deletion if required | Immediate action supported by automated triggers |
Automating these safeguards enhances compliance, especially as regulations evolve.
Using Technology for Consent Management
Automation is key to maintaining compliance across multiple frameworks. Manual processes often lead to delays and errors, making it harder to handle consent effectively. Using technology platforms designed for consent management can streamline these tasks, ensuring accuracy and consistency [13].
Take Censinet RiskOps™ as an example. This platform helps healthcare organizations manage consent records, track withdrawal requests, and ensure compliance with various frameworks - all from one centralized system. It automates critical tasks like collecting consent with audit trails, managing breach notifications to meet specific timelines, and enforcing access controls tied to consent status. Plus, integrated analytics highlight consent trends, helping organizations spot and address potential gaps before they lead to compliance issues [13][15].
To complement these tools, organizations should have clear workflows for consent management. Define roles for who collects, reviews, and approves consent, as well as who handles withdrawal requests. Detailed documentation of timelines for each step ensures these processes remain consistent and scalable, even as the organization grows [13]. By formalizing these workflows, you can avoid the pitfalls of informal or inconsistent practices.
How to Map and Document Patient Consent
To ensure compliance with regulations like HIPAA and GDPR, a well-structured consent inventory is essential. This inventory helps track where patient consent is collected, how it's used, and where it's shared, reducing uncertainty in compliance efforts.
Building a Consent Inventory
Start by identifying every point where patient consent is either required or recorded. This means mapping all data collection methods, classifying the types of information gathered, detailing downstream processing activities, and documenting the legal basis for each data flow. This approach ties regulatory policies directly to day-to-day operations.
Your inventory should clearly define what each authorization covers. For instance, does the patient allow access to their entire medical record, or just specific sections? Additionally, it should specify who is authorized to access this data - whether it's the patient, legal representatives, or third parties. The inventory must also account for the specific requirements of different frameworks, such as GDPR’s need for explicit consent in non-direct care scenarios and HIPAA’s allowances for disclosures related to treatment or operations. Utilizing tools like the NIST Privacy Framework v1.0 (Identify-P function) can provide structure to your mapping process, making it easier to navigate overlapping regulations while reducing third-party risk.
A detailed consent inventory also sets the stage for automating consent tracking, which will be discussed further in the next section.
Maintaining Consent Records and Monitoring Compliance
Consent records must include timestamps and version histories to meet HIPAA’s six-year retention rule and GDPR’s documentation standards [2]. GDPR also mandates that withdrawing consent must be as simple as granting it.
Automating consent recordkeeping is key to avoiding errors and fragmented data. Tools like Censinet RiskOps™ offer centralized systems that handle consent records, including timestamps, collection points, and applicable privacy policies. This eliminates the inefficiencies of manual tracking. For example, Tower Health used Censinet RiskOps™ to streamline its processes, reallocating three full-time employees to other tasks and boosting risk assessments while reducing manual workloads [17].
When a patient withdraws consent or invokes GDPR’s "right to be forgotten", ensure that all connected systems are updated promptly. This involves identifying every location where the patient’s data resides, whether across affiliates or software platforms. Failure to act quickly can lead to compliance issues, as regulations set strict timeframes for these updates.
Regular monitoring is essential to ensure that technical systems align with recorded consent preferences. For instance, tracking tools should not activate before consent is granted or continue after a user opts out. Routine audits can catch and correct discrepancies before they lead to violations. These audits often include third-party risk assessment questions to ensure external vendors remain compliant. Considering the steep penalties - up to nearly $2,000,000 annually under HIPAA and as much as €20 million or 4% of global revenue under GDPR - investing in reliable consent management systems is not just prudent, it’s necessary [18][16].
Conclusion
Handling patient consent within the frameworks of HIPAA, GDPR, and similar regulations demands constant attention and adjustment. Mismanaging consent can lead to major consequences for healthcare organizations, including hefty financial penalties - HIPAA violations average $1.5 million per case, while GDPR fines can reach as high as 4% of global revenue or €20 million. Beyond financial losses, the impact on individuals is staggering: in 2023 alone, 133 million people in the US were affected by data breaches, with 45% of those breaches tied to issues like improper consent management or access controls [19][20]. The stakes are undeniably high.
Adopting advanced technologies can significantly reduce these risks. For example, a 2024 Ponemon Institute study found that organizations using automated consent management platforms saw a 62% drop in compliance violations and a 40% reduction in audit durations [21]. Tools like Censinet RiskOps™ offer centralized solutions for maintaining consent records, conducting third-party risk assessments, and strengthening overall cybersecurity efforts. These capabilities are essential for safeguarding patient data and ensuring the protection of sensitive health information (PHI).
FAQs
How do I choose the right legal basis for processing health data under GDPR?
When processing health data under GDPR, healthcare organizations need to determine the correct legal basis. One option is obtaining explicit patient consent. Another valid basis is if the processing is essential for treatment, payment, or healthcare operations. Even in these cases, organizations must strictly follow GDPR guidelines to remain compliant.
What should I do if an EU patient asks to delete their data but HIPAA requires record retention?
Healthcare organizations face a complex challenge when an EU patient requests data deletion. This situation requires carefully navigating between the GDPR's "right to erasure" and HIPAA's record retention requirements.
Under GDPR, individuals have the right to request the deletion of their personal data. However, HIPAA mandates that healthcare providers retain certain medical records for a legally defined period, often several years. This can make immediate data deletion impossible in some cases.
The key here is transparency. When such a request arises, healthcare organizations should clearly inform the patient about HIPAA's legal obligations. Explain that while you respect their GDPR rights, specific records must be retained to comply with U.S. law. Assure them that any data not subject to these retention rules will be reviewed for deletion as soon as possible.
By addressing both legal frameworks thoughtfully, you can maintain compliance while fostering trust with the patient.
What’s the simplest way to manage consent across HIPAA, GDPR, and CCPA at the same time?
Managing consent under HIPAA, GDPR, and CCPA can be challenging, but a unified system can help meet the strictest requirements of each regulation. To start, GDPR demands clear opt-in consent, ensuring individuals actively agree to data collection and use. HIPAA, on the other hand, involves both implied and explicit authorizations, depending on the situation, particularly for healthcare-related data. Meanwhile, CCPA emphasizes transparency and gives users the right to opt out of the sale of their information.
Using a centralized platform can make this process more manageable. Features like dynamic consent management, detailed audit trails, and automation not only simplify compliance but also reduce the chance of mistakes. Plus, staying ahead of evolving regulations while safeguarding patient trust becomes much easier with such a system in place.


