HIPAA Incident Response Plan: Key Requirements
Post Summary
To protect sensitive patient data and comply with HIPAA regulations, healthcare organizations must have a clear incident response plan. Here's what you need to know:
- HIPAA Security Rule (§164.308(a)(6)) mandates organizations to detect, contain, and resolve security incidents impacting electronic protected health information (ePHI).
- Breach Notification: Notify affected individuals and the HHS Secretary within 60 days of discovering a breach.
- Key Components:
- Risk Assessments: Regularly evaluate risks and maintain an inventory of devices handling ePHI.
- Roles and Responsibilities: Assign a Security Official and define roles like Privacy Officer, IT Lead, and Legal Counsel.
- Incident Detection: Use tools like SIEM and Endpoint Detection to monitor threats.
- Response Phases: Follow structured steps - detection, containment, eradication, and recovery.
- Documentation: Keep detailed records of incidents for at least six years.
Organizations face challenges like third-party vendor risks, staff training gaps, and juggling multiple regulations. Tools like Censinet RiskOps™ can simplify compliance with automated risk assessments and AI-driven investigations.
Bottom Line: A robust HIPAA incident response plan safeguards patient data, ensures compliance, and minimizes operational disruptions.
HIPAA and Incident Response: How to Manage Security Incidents in a HIPAA-Compliant Environment.
sbb-itb-535baee
Required Elements of a HIPAA-Compliant Incident Response Plan
Creating a HIPAA-compliant incident response plan requires strict alignment with federal regulations. According to 45 CFR Section 164.308 of the HIPAA Security Rule, organizations must establish formal procedures to identify, respond to, and document security incidents involving electronic protected health information (ePHI). Failure to comply can lead to hefty penalties.
Risk Assessments and Asset Inventories
To safeguard ePHI, organizations must regularly conduct risk assessments and maintain up-to-date asset inventories. These inventories should include all devices and platforms that handle ePHI, such as servers, workstations, mobile devices, and cloud storage. HIPAA mandates that documentation of security incidents and risk assessments be retained for at least six years from their creation date [1].
When an incident occurs, a four-factor risk assessment determines whether it must be reported. This assessment evaluates:
- The nature and sensitivity of the PHI involved.
- The identity of the unauthorized person who accessed or received the information.
- Whether the PHI was actually acquired or viewed.
- The extent to which the risk has been mitigated.
Accurate and comprehensive asset inventories are essential for conducting thorough breach evaluations.
Roles and Responsibilities
A compliant plan must designate a Security Official to oversee its development and implementation. Beyond this, specific roles should be assigned to address technical, legal, and communication responsibilities. For example:
- Privacy Officer: Conducts the four-factor risk assessment.
- IT Lead: Isolates affected systems and preserves forensic evidence.
- Legal Counsel: Manages regulatory reporting deadlines.
- Communications Lead: Handles media notifications for breaches impacting 500 or more individuals.
"The plan must define the roles and responsibilities of the Incident Response Team, including a designated Security Official and individuals responsible for technical, legal, and communication tasks." - LegalClarity Team [1]
External partners, such as forensic experts and law enforcement, play a vital role in incident response. Keep contact lists for these resources up to date to ensure rapid activation when needed. Additionally, HIPAA requires workforce training, so regular sessions should be scheduled to familiarize staff with their responsibilities and escalation procedures. Clear role assignments, combined with effective training, help build a strong foundation for detecting and managing incidents.
Incident Detection and Monitoring
Accurate inventories and well-defined roles are key to effective incident detection. HIPAA defines a security incident broadly, covering any attempt or success in unauthorized access, use, disclosure, modification, or destruction of information. To catch these incidents early, organizations should deploy advanced monitoring tools like Security Information and Event Management (SIEM) systems and Endpoint Detection and Response (EDR) solutions. These tools provide continuous surveillance, helping to identify suspicious activity before it escalates.
Your plan must outline procedures for quickly isolating affected systems to limit unauthorized access and prevent data loss [1]. Prompt containment is critical - delays can expand the breach's impact and increase notification requirements. Additionally, establish protocols for forensic analysis and evidence preservation to determine the scope and details of the incident accurately. This documentation is essential when reporting to the Department of Health and Human Services (HHS) and notifying affected individuals within the required 60-day window for breaches involving 500 or more people [1].
Incident Response Phases: Detection to Recovery
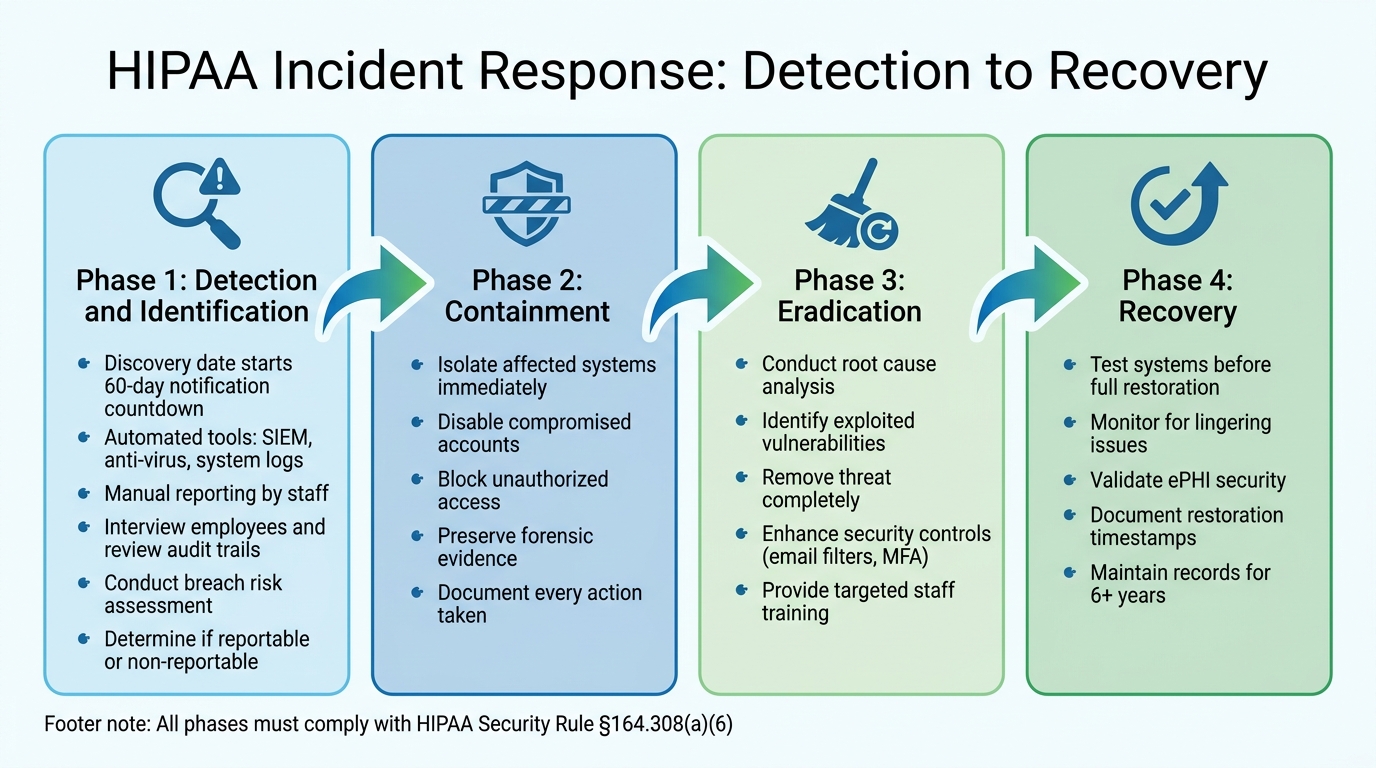
HIPAA Incident Response: 4-Phase Process from Detection to Recovery
Handling a HIPAA security incident effectively requires a well-structured approach, starting from the moment it's detected through to full recovery.
Detection and Identification
The first step in responding to an incident is discovery. Under HIPAA, "discovery" marks the day an incident is either known or should reasonably have been known by your organization. This moment is pivotal because it starts the 60-day countdown for notifying affected parties in the case of reportable breaches. Early detection is, therefore, a top priority.
Incidents are usually detected through two primary methods: automated security tools and manual reporting by staff. Automated tools - like anti-virus alerts, SIEM platforms, and system logs - spot unusual activity, while manual reporting can uncover physical or operational security issues. Both approaches work together to ensure a robust detection process.
Once a potential incident is flagged, a detailed investigation follows. This includes interviewing employees, reviewing audit trails, and analyzing system logs to confirm whether a violation occurred. HIPAA’s Security Rule mandates that systems containing electronic protected health information (ePHI) have mechanisms to record and examine activity (§164.312(b)) [2][4].
A key part of this phase is assessing the severity of the incident. Using a breach risk assessment framework helps determine whether the incident requires formal breach notification or can be classified as a non-reportable event. This decision triggers the appropriate notification process under HIPAA. Centralizing reports through a single channel, like a Privacy Office or Security Officer, can streamline prioritization and identify recurring vulnerabilities that may call for updated safeguards or specialized training.
After identifying the issue, the next steps - containment and eradication - are crucial to minimizing further damage.
Containment, Eradication, and Recovery
Quickly implementing short-term containment measures is essential to stop the incident from spreading. This might involve isolating affected systems, disabling compromised accounts, or blocking unauthorized access. It’s critical to preserve forensic evidence during this phase and document every action taken. These records are vital for both regulatory reporting and understanding what went wrong.
Once the immediate threat is contained, a deeper investigation is needed to uncover how the breach occurred and which vulnerabilities were exploited. This root cause analysis shapes the eradication strategy. For instance, if a phishing attack was the entry point, remediation could include enhancing email filters, rolling out multi-factor authentication, and offering targeted security training to employees.
Recovery focuses on bringing systems back to normal operation while ensuring the threat has been completely neutralized. Before systems are fully restored, test and monitor them for any lingering issues to ensure ePHI is secure. Every step of the recovery process, including validation checks and the exact date and time systems are back online, should be documented.
Once recovery is complete, thorough documentation ensures compliance and helps improve future incident response efforts.
Documentation and Audit Trails
Comprehensive documentation is a cornerstone of HIPAA compliance. Organizations are required to maintain incident reports and risk assessments for at least six years [2][3][4]. This documentation not only demonstrates compliance during audits but also provides a clear record of how breach decisions were made and serves as a resource for refining response strategies.
Key details to document include who discovered the incident, when it was detected, which systems were involved, and whether any PHI was accessed or exposed. Include timestamps, names of team members involved, and the reasoning behind critical decisions made during the breach risk assessment. This level of detail not only protects the organization legally but also helps uncover patterns that might point to broader security vulnerabilities needing attention.
HIPAA Breach Reporting and Notification Requirements
Once a breach is confirmed, the clock starts ticking on notification deadlines. Missing these deadlines can lead to hefty penalties, so having well-defined notification procedures is crucial for addressing HIPAA breaches effectively.
Breach Notification Timelines
The notification timeline begins on the discovery date - the day your organization becomes aware of the breach or should have reasonably known about it. From that point, notifications must be sent within 60 days, regardless of the breach size [5].
"Individual notifications must be provided without unreasonable delay and in no case later than 60 days following the discovery of a breach." - HHS.gov [5]
The scale of the breach determines additional reporting requirements, as outlined below:
| Notification Recipient | Breach Size/Condition | Mandatory Timeline |
|---|---|---|
| Affected Individuals | Any size breach of unsecured PHI | Max 60 days after discovery [5] |
| HHS Secretary | 500+ individuals affected | Max 60 days after discovery [5] |
| HHS Secretary | Fewer than 500 individuals affected | Max 60 days after the end of the calendar year [5] |
| Media Outlets | 500+ residents in a state/jurisdiction | Max 60 days after discovery [5] |
Notifications should be sent via first-class mail or, if the individual has opted in, by email. If contact information for 10 or more individuals is outdated, you must post a notice on your website’s homepage for at least 90 days and provide a toll-free number that remains active during this period [5]. For breaches involving business associates, the associate must promptly notify the covered entity to ensure the entity meets its own notification requirements [5].
Staying on top of these timelines requires seamless coordination and communication within your organization.
Internal and External Communication
Internally, ensure that your Privacy Officer, Security Officer, legal team, and executive leadership are immediately informed to facilitate quick decision-making on containment and remediation. Designating a single point of contact for managing incident communication helps maintain clarity and consistency across departments.
Externally, things get more intricate. If a business associate identifies a breach, they are responsible for providing the covered entity with the names of affected individuals so that notifications can be issued [5]. Your Business Associate Agreements (BAAs) should clearly define these responsibilities to prevent delays. Preparing notification letters and media response templates in advance can save critical time. These templates should include:
- A detailed description of the breach
- The types of information involved
- Steps individuals can take to protect themselves
- Your investigation and remediation actions
- Contact information for questions or concerns
Make sure to document every notification, including timestamps and delivery methods. Your organization must be able to prove compliance, and this documentation - kept for at least six years - will be essential if regulators scrutinize your response [5].
These structured protocols set the stage for effective incident management. In the next section, we’ll look at how tools like Censinet RiskOps™ can streamline your response efforts.
Using Censinet RiskOps™ for HIPAA Incident Response

Managing HIPAA incidents manually can drain resources and leave room for missed deadlines. That's where Censinet RiskOps™ steps in. Designed specifically for healthcare organizations, this platform simplifies risk assessments, accelerates investigations, and brings everything under one streamlined system.
Automated Risk Assessments and Continuous Monitoring
Censinet RiskOps™ takes the hassle out of vendor and asset risk scoring by automating the process with standardized questionnaires and real-time data. Instead of spending hours on manual evaluations, the platform scores risks based on HIPAA Security Rule criteria, such as exposure to protected health information (PHI). This proactive system spots vulnerabilities early, helping prevent breaches before they happen.
For example, Intermountain Healthcare used Censinet RiskOps™ in Q1 2024 to evaluate 500 vendors. The results? They identified critical risks in 15% of them. With CISO Mark Jones leading the charge, the organization sped up risk scoring by 50% and took immediate action during a ransomware attack, avoiding reportable breaches and saving about $1.2 million [8].
The platform’s continuous monitoring tools take oversight to the next level. Real-time dashboards and API integrations track asset inventories, flag unusual activity in access logs, and work seamlessly with SIEM tools for around-the-clock surveillance. When unauthorized access occurs, instant alerts from EHR system integrations ensure compliance with HIPAA's security requirements under 45 CFR § 164.308(a)(1) [7]. Healthcare providers using Censinet RiskOps™ have reported a 70% reduction in third-party risk assessment time and a 40% improvement in breach detection speed [6].
By automating these processes, healthcare organizations can respond faster and more effectively to potential threats.
AI-Driven Incident Investigation Tools
Censinet AI™ revolutionizes breach investigations by cutting the process from days to mere hours. Powered by machine learning, it consolidates logs, network traffic, and activity data into a single timeline, automatically tagging evidence to maintain chain-of-custody compliance. This approach slashes manual investigation time by up to 70%, helping organizations meet HIPAA's 60-day notification deadline [9].
A real-world example: In September 2023, Cleveland Clinic faced a phishing attack affecting 10,000 PHI records. With Censinet AI™, their team completed the investigation in just two days instead of the usual ten. Dr. Lisa Patel, who led the project, noted 90% accuracy in pinpointing the root cause, allowing for timely notification to HHS and avoiding penalties [11]. The platform’s natural language processing lets teams query incident data conversationally, while its predictive analysis estimates breach scope and generates HHS-compliant reports with a single click [10].
During a ransomware attack targeting patient records, Censinet AI™ analyzed 10TB of logs in minutes, pinpointing the 50,000 affected PHI records. It prioritized containment actions and delivered an audit-ready report, reducing recovery costs by 30% compared to traditional methods [11].
These tools not only speed up investigations but also provide actionable insights for immediate response.
Centralized Dashboards for Risk Management
Censinet's centralized dashboards bring everything into focus with role-based views, real-time risk scores, incident trackers, and compliance alerts. This setup speeds up decision-making by 25% during active incidents [12].
The dashboards are designed for collaboration, offering shared workspaces for incident playbooks, risk discussions, and executive summaries tailored for board presentations. Roles can be assigned according to HIPAA's workforce security standards, ensuring that the right people access the right information at the right time [13]. For organizations juggling hundreds of vendors, the benchmarking feature compares your risk profile to industry peers, helping you prioritize which third parties need immediate attention.
To get started, healthcare organizations can roll out the platform in phases: begin with automated assessments, then enable continuous monitoring, and finally, customize dashboards to fit your workflows. Most organizations see a return on investment within 3 to 6 months, all while minimizing disruption to existing operations.
Conclusion and Next Steps
A strong HIPAA-compliant incident response plan does more than just protect patient data - it safeguards your organization's reputation. With 133 million individuals impacted by data breaches in 2023 and 89% of healthcare organizations experiencing at least one cyber incident in 2024 [14][15], preparation isn’t optional - it’s critical.
Best Practices Summary
To stay ahead of threats, make regular updates to your risk assessments, asset inventories, and role assignments. Use continuous monitoring and detection tools to identify risks early. Follow a structured response process - starting with detection, moving through containment and eradication, and finishing with recovery - all while keeping detailed, audit-ready documentation. Don’t forget HIPAA’s breach notification requirement, which demands reporting incidents within 60 days [6][7].
Preparation pays off in measurable ways. Organizations with well-developed incident response plans reduce response times by 50%, saving an average of $4.45 million per incident [7][10]. However, only 26% of healthcare providers have achieved this level of readiness [16]. This underscores the importance of regular tabletop exercises and simulations to uncover and address vulnerabilities [17].
Once you’ve covered these basics, focus on targeted actions to further strengthen your incident response.
How to Improve Your Incident Response
To take your plan to the next level, start with a thorough audit against HHS guidelines and conduct a gap analysis using updated risk assessments. Simulated breach exercises can test your team’s readiness under pressure, while regular updates to notification protocols ensure compliance with the latest regulations. Make it a habit to review and refine your plan quarterly, using insights from past incidents to close any gaps [18].
For organizations looking to streamline these efforts, Censinet RiskOps™ offers a powerful solution. This platform automates risk assessments, provides AI-driven investigative tools, and delivers centralized dashboards for real-time oversight. Users report 40% faster incident resolution and better compliance outcomes during HHS audits [7]. Its phased approach - starting with automated assessments, followed by continuous monitoring and custom dashboards - addresses critical weaknesses in detection and recovery while aligning with HIPAA requirements.
FAQs
What is the difference between a HIPAA security incident and a reportable breach?
A HIPAA security incident occurs when there’s unauthorized access to or disclosure of Protected Health Information (PHI). However, it might not require reporting if a thorough risk assessment determines there’s minimal harm involved. On the other hand, a reportable breach involves improper use or disclosure of unsecured PHI that jeopardizes its privacy or security. In such cases, HIPAA mandates notifying affected individuals within 60 days and strictly following its breach notification requirements.
How is the breach “discovery date” determined for the 60-day deadline?
The breach discovery date marks the moment a breach is first identified or detected. This date is critical because it triggers the 60-day countdown to comply with HIPAA’s notification requirements. Documenting this date accurately is essential to ensure all compliance deadlines are met without issue.
What documentation is required for HIPAA incident response audits?
Organizations are required to keep thorough documentation of all incident details, risk assessments, breach notifications, response actions, and training logs. To meet HIPAA compliance standards, these records must be retained for a minimum of six years.


