HIPAA vs GDPR: PHI Data Transfer Rules
Post Summary
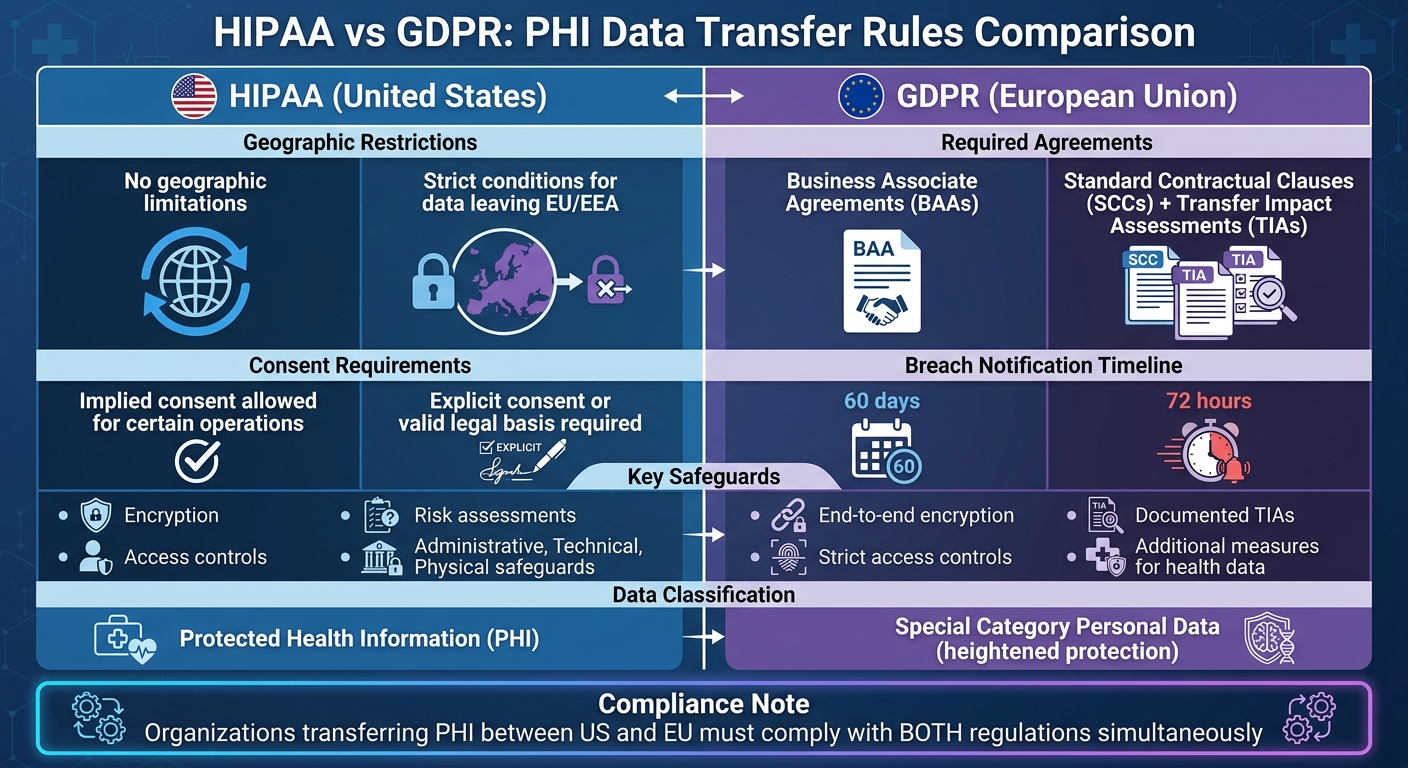
Healthcare organizations transferring Protected Health Information (PHI) between the U.S. and the EU must comply with two key regulations: HIPAA (U.S.) and GDPR (EU). Here’s what you need to know:
- HIPAA focuses on protecting PHI within the U.S. and allows international transfers if safeguards like encryption and Business Associate Agreements (BAAs) are in place.
- GDPR applies to any organization processing EU residents' data, requiring stricter rules for international transfers, such as Standard Contractual Clauses (SCCs) and Transfer Impact Assessments (TIAs).
- Key differences:
- HIPAA has no geographic restrictions, while GDPR imposes strict conditions for data leaving the EU.
- HIPAA allows implied consent for certain operations, but GDPR demands explicit consent or a valid legal basis for processing sensitive data.
- Breach notification deadlines differ: HIPAA allows 60 days, while GDPR mandates 72 hours.
For compliance, organizations must map data flows, establish legal agreements (BAAs for HIPAA, SCCs for GDPR), and implement security measures like encryption. Using tools like Censinet RiskOps™ can simplify managing these requirements across jurisdictions.
HIPAA vs GDPR PHI Transfer Requirements Comparison
HIPAA Rules for International PHI Transfers
HIPAA's Lack of Data Residency Requirements
Unlike many international privacy laws, HIPAA doesn't impose restrictions on where protected health information (PHI) can be stored. There are no geographic limitations - PHI can be transferred and stored in any country, even those with weaker privacy protections. As Gil Vidals, CEO of HIPAA Vault, explains:
"HIPAA's reach is defined by the origin of the PHI and the entities handling it - not their geographic location." [4]
For example, a U.S. hospital is permitted to store PHI on cloud servers located anywhere in the world. HIPAA's protections follow the data itself, regardless of where it's stored [3][4]. The regulation doesn't focus on borders but instead emphasizes ensuring that adequate safeguards are in place. The Department of Health and Human Services (HHS) crafted the Security Rule to be "flexible, scalable, and technology neutral", allowing entities to adopt measures tailored to their size, structure, and specific risks [1].
Because PHI often moves across borders, it's critical to implement strong security measures when handling international transfers.
Required Safeguards for Transferred PHI
While HIPAA allows PHI to be stored globally, transferring it internationally comes with strict security requirements. Before sharing electronic PHI (ePHI) with a foreign vendor, covered entities must establish a Business Associate Agreement (BAA). This agreement ensures that HIPAA's Privacy and Security Rule protections extend to the foreign business partner [1][3].
HIPAA's Security Rule outlines three main categories of safeguards:
- Administrative safeguards: These include conducting third-party risk assessments to identify potential vulnerabilities in international transfers, providing HIPAA training for overseas personnel, and requiring subcontractors to include "flow-down" clauses in their contracts to uphold HIPAA standards.
- Technical safeguards: Organizations must use encryption and access controls to secure data. Examples include TLS encryption for data in transit, AES encryption for data at rest, role-based access control (RBAC), multi-factor authentication (MFA), and audit logging to track PHI access [1][2][4].
- Physical safeguards: This involves controlling access to facilities, as well as securely managing and disposing of hardware or media that contains ePHI [1].
Entities must also adhere to the "minimum necessary" standard, ensuring only the specific PHI fields required for a task are shared during international transfers. For administrative access across borders, secure transmission methods like VPNs, SFTP, or TLS-encrypted email should be used. Additionally, HIPAA requires that all documentation, including policies and BAAs, be retained for six years from their creation or last use [1].
These guidelines provide a framework for securely managing international PHI transfers, setting the stage for a comparison with GDPR's stricter regulations in the next sections.
sbb-itb-535baee
GDPR Rules for International PHI Transfers
Chapter V Restrictions on Data Transfers
The GDPR enforces strict rules for transferring personal data, including health-related information, beyond the European Economic Area (EEA) or the UK. According to Article 44, such transfers are only allowed if they meet the criteria outlined in Chapter V, ensuring that data receives the same level of protection as it would within the EEA.
There are two primary pathways for lawful international transfers:
- Adequacy Decisions: These apply when a destination country has been recognized as offering GDPR-equivalent protection. For example, the UK and certain U.S. organizations certified under the EU-US Data Privacy Framework fall into this category.
- Appropriate Safeguards: This includes mechanisms like Standard Contractual Clauses (SCCs) or Binding Corporate Rules (BCRs). SCCs are pre-approved legal terms that assign clear data protection obligations, while BCRs are tailored for multinational corporations but involve lengthy approval processes, often taking one to two years.
However, following the Schrems II ruling, simply using SCCs isn't enough. Organizations must conduct a Transfer Impact Assessment (TIA) to determine if the destination country's legal environment - particularly regarding government surveillance - compromises the safeguards. For instance, in May 2023, Meta Platforms Ireland Limited faced a €1.2 billion fine from the Irish Data Protection Commission. The penalty stemmed from Meta's failure to adequately address risks highlighted in Schrems II, despite using SCCs. Meta was also ordered to stop unlawfully processing and storing EU/EEA user data in the U.S. [7].
Article 49 provides limited exceptions for transfers, such as cases involving explicit consent or vital interests. However, these exceptions are unsuitable for routine data transfers, making them impractical for most healthcare organizations.
These stringent rules underline the need for additional safeguards when handling health data.
Additional Safeguards for Health Data
Under the GDPR, health data is classified as a special category of personal data, warranting extra protection. Unlike HIPAA, which often permits implied consent for healthcare operations, GDPR requires explicit consent or another valid legal basis for processing health data, including international transfers.
When transferring health data across borders, organizations must go beyond basic transfer mechanisms like SCCs or adequacy decisions. They should integrate supplementary measures such as:
- End-to-end encryption to protect data during transmission.
- Strict access controls to limit who can view or handle the data.
- Documented TIAs that specifically address the heightened sensitivity of health information.
The European Data Protection Board stresses that:
"data exporters are responsible for monitoring whether adequacy decisions relevant to their transfers are still in force and not in the process of being revoked or invalidated" [6].
Healthcare organizations must review their entire third-party risk across their vendor network to identify any third parties processing health data outside the EEA/UK. This includes cloud service providers, especially when support or monitoring involves access from non-adequate countries. For transfers to the U.S., organizations should ensure recipients are self-certified under the EU-US Data Privacy Framework by checking the International Trade Administration's public registry. Additionally, any onward transfers to other entities must be covered by equivalent safeguards, creating a robust chain of accountability.
These technical and contractual safeguards must be seamlessly integrated into broader compliance efforts to ensure full adherence to GDPR requirements.
Data Protection in the US vs in the EU - GDPR vs HIPAA
Key Differences Between HIPAA and GDPR for PHI Transfers
Let’s dive into how HIPAA and GDPR differ when it comes to handling international PHI transfers.
Transfer Mechanisms and Restrictions Compared
HIPAA takes a more flexible approach, allowing global transfers of PHI as long as proper safeguards are in place. For example, a U.S. hospital can send patient records to another country by using Business Associate Agreements (BAAs). These agreements ensure that the receiving party adheres to HIPAA’s privacy and security standards.
In contrast, GDPR imposes stricter rules. Health data cannot leave the European Economic Area (EEA) or UK unless the destination country meets certain conditions, like having an adequacy decision. If no such decision exists, organizations must rely on approved mechanisms such as Standard Contractual Clauses (SCCs) or Binding Corporate Rules (BCRs). However, since the 2020 Schrems II ruling, SCCs alone aren’t enough. Organizations must now also conduct Transfer Impact Assessments (TIAs) to determine if the destination country’s laws might undermine GDPR protections.
Another key difference lies in consent requirements. HIPAA generally doesn’t require patient consent for transfers to business associates, while GDPR demands explicit consent or another legal basis for processing sensitive health data.
| Aspect | HIPAA | GDPR |
|---|---|---|
| Transfer Restrictions | No geographic limits if safeguards are met | Strict; requires mechanisms for transfers outside EEA |
| Required Agreements | BAAs | SCCs, BCRs, or adequacy decisions |
| Consent Role | Authorization for disclosures, not transfers | Explicit consent or legal basis for sensitive data |
| Country Prohibitions | None | Blocked without approved mechanisms |
These differences create challenges for organizations managing compliance across jurisdictions. For instance, a U.S. hospital working with an EU-based analytics vendor must comply with both frameworks. This means executing a BAA for HIPAA compliance and SCCs with a TIA for GDPR compliance. Even if a transfer meets HIPAA standards, it could still violate GDPR if sent to a high-risk country like China without additional safeguards.
Breach notification timelines further highlight the divergence between these frameworks.
Breach Notification Requirements
HIPAA and GDPR also vary significantly in how they handle breach notifications. HIPAA allows up to 60 days to notify affected parties in breaches involving 500 or more individuals. GDPR, however, requires notification within just 72 hours of discovering a breach. This creates a much tighter window for incident response under GDPR.
For cross-border incidents, this timing difference can become a major challenge. For example, if a breach occurs during an EU-U.S. data transfer, GDPR’s 72-hour clock starts immediately. Meanwhile, for the same incident, HIPAA would allow 60 days to notify affected individuals. To manage this, organizations often rely on automated monitoring systems to detect breaches quickly and meet GDPR’s stricter timeline while also preparing HIPAA-compliant documentation.
The financial stakes are high. By 2024, GDPR fines for data transfer violations totaled €2.7 billion, with the healthcare sector accounting for 15% of cases. HIPAA penalties, on the other hand, averaged $1.5 million per violation in 2023. Risk assessment obligations also differ: HIPAA focuses on whether a breach poses a significant risk based on factors like data sensitivity and the likelihood of harm. GDPR takes a broader view, requiring evaluation of any compromise to personal data integrity, regardless of risk thresholds.
To streamline compliance, many healthcare organizations adopt unified incident response plans that default to GDPR’s stricter timeline. Tools like Censinet RiskOps™ help by providing real-time risk tracking across multiple jurisdictions, enabling organizations to meet both HIPAA and GDPR requirements without maintaining separate breach management processes.
Compliance Strategies for Healthcare Organizations
Healthcare organizations face a complex challenge when managing international transfers of Protected Health Information (PHI). To meet both HIPAA and GDPR requirements, a structured approach is essential. This includes mapping all data flows, implementing proper legal mechanisms, and conducting regular risk assessments to ensure compliance across different jurisdictions.
Conducting Transfer Impact Assessments (TIAs)
The Schrems II ruling introduced new requirements for organizations using Standard Contractual Clauses (SCCs). One key requirement is conducting Transfer Impact Assessments (TIAs) to ensure that destination countries provide adequate data protection. TIAs evaluate whether a country’s laws, such as U.S. FISA Section 702, grant government access to data in a way that goes beyond what is necessary or proportionate, and whether individuals have effective legal remedies in those jurisdictions [8].
Start by mapping all data transfers, including any onward flows. Before diving into a full TIA for a U.S.-based vendor, check their certification status at dataprivacyframework.gov. If the vendor is certified under the EU-U.S. Data Privacy Framework (adopted in July 2023), the transfer may fall under the adequacy decision, potentially eliminating the need for a full TIA [8].
When a TIA reveals potential risks, implement additional safeguards to protect the data. Technical measures like end-to-end encryption, pseudonymization, or zero-knowledge architecture can prevent international importers from accessing unencrypted PHI. These measures also align with HIPAA’s Security Rule, creating a unified approach to data protection that addresses both GDPR and HIPAA requirements [8].
Document each TIA thoroughly, outlining the factors assessed and any safeguards applied. This documentation demonstrates accountability under GDPR and can serve as evidence during regulatory reviews. Reassess TIAs regularly or whenever there are changes in destination country laws, SCC amendments, or new guidance from the European Data Protection Board (EDPB) or national authorities [8].
TIAs establish a baseline for data protection, but organizations also need to align legal agreements for seamless compliance.
Integrating SCCs and BAAs
Healthcare organizations working with cloud vendors must manage both GDPR’s SCCs and HIPAA’s Business Associate Agreements (BAAs). For controllers working with processors, the 2021 EU SCCs Module 2 (Controller-to-Processor) is the standard requirement [8].
The 2021 SCCs include mandatory terms that cannot be altered. When combining SCCs with BAAs, make sure the BAA terms don’t conflict with the SCCs, as the SCCs generally take precedence in data transfer arrangements. Replace any outdated SCC versions with the mandatory 2021 version to avoid enforcement actions [8].
For U.S.-based vendors, check their certification under the Data Privacy Framework. If certified, SCCs may not be strictly necessary for the transfer itself, but a BAA is still required under HIPAA [8]. For vendor-to-sub-vendor PHI transfers, ensure your primary vendors use equivalent transfer mechanisms with their sub-processors, such as SCC Module 3 (Processor-to-Processor) [8].
"SCCs must be executed between each pair of data exporter and data importer... each bilateral relationship needs its own executed agreement." - ECOSIRE Research and Development Team [8]
This highlights the stricter controls under GDPR compared to HIPAA and underscores the need for cohesive transfer protocols. Consolidating HIPAA and GDPR compliance efforts into a single evidence repository can simplify the process [9]. Additionally, include transparency clauses in contracts, requiring data importers to notify you of any legally binding government requests for data disclosure [8].
Once agreements and safeguards are in place, automated tools can help manage ongoing compliance.
Using Censinet RiskOps™ for Risk Management
Automated risk management tools like Censinet RiskOps™ simplify compliance across jurisdictions. The platform centralizes compliance monitoring, automates risk assessments, and organizes documentation for both HIPAA and GDPR requirements.
Censinet RiskOps™ supports continuous monitoring of vendor relationships, which is critical since TIAs must be updated when destination country laws change or when new regulatory guidance is issued. With Censinet AI™, vendors can complete security questionnaires in seconds, providing summaries of vendor evidence, product integration details, and even fourth-party risk exposures.
For organizations with complex sub-processor chains, the platform offers visibility into onward transfers. This ensures that primary vendors maintain proper transfer mechanisms with their sub-processors. The platform’s command center provides a clear view of risks across the entire vendor ecosystem, helping organizations identify which transfers require SCCs, BAAs, or both. This approach also supports the maintenance of Records of Processing Activities (ROPA) and ensures that SCCs and TIA documentation are readily available for regulatory inspections [8].
Designed specifically for healthcare cybersecurity and risk management, Censinet RiskOps™ helps organizations manage the intricacies of PHI compliance across multiple regulatory frameworks while maintaining a centralized repository for all compliance-related evidence.
Conclusion
Transferring Protected Health Information (PHI) internationally brings unique compliance challenges. HIPAA allows cross-border data sharing if proper safeguards and Business Associate Agreements (BAAs) are in place. On the other hand, the GDPR sets a higher bar, requiring either an adequacy decision or specific mechanisms like Standard Contractual Clauses (SCCs). While HIPAA focuses on strong security measures regardless of location, GDPR demands that the destination country’s legal system ensures sufficient data protection.
To navigate these complexities, align your approach by leveraging GDPR-compliant transfer tools, HIPAA-level security measures, and maintaining a detailed inventory of data flows [5]. This strategy supports compliance with both frameworks and keeps operations running smoothly.
Technical safeguards play a critical role in ensuring compliance. Using advanced encryption, tokenization, and regional processing enclaves minimizes risks while meeting HIPAA’s Security Rule and GDPR’s additional requirements. These measures work in tandem with legal agreements that incorporate SCCs and BAAs, avoiding jurisdictional conflicts.
Censinet RiskOps™ simplifies compliance by automating the monitoring of cross-border data routing, encryption practices, and subprocessor updates. It also helps identify and prevent unauthorized "shadow transfers." With the added capabilities of Censinet AI™, organizations can expedite vendor assessments and gain better visibility into fourth-party risks, ensuring continuous oversight across their vendor networks.
Successfully managing international PHI transfers requires precise data classification, thorough Transfer Impact Assessments (TIAs), and automated compliance tools. By combining legal frameworks, technical defenses, and specialized risk management systems, healthcare organizations can safeguard patient information and confidently operate across various jurisdictions in a shifting regulatory environment.
FAQs
When do I need SCCs vs the EU-U.S. Data Privacy Framework for PHI?
Healthcare organizations that need to transfer Protected Health Information (PHI) internationally should consider using Standard Contractual Clauses (SCCs). These clauses are essential for transfers from the EU to non-EU countries, including the U.S., especially when a more adaptable legal solution is required. While the EU-U.S. Data Privacy Framework simplifies EU-to-U.S. transfers, its scope is limited. SCCs are the go-to option when the Framework cannot be applied or isn’t available.
Do I need both a BAA and SCCs for the same vendor transfer?
For international transfers of Protected Health Information (PHI), you usually need two key agreements: a Business Associate Agreement (BAA) and Standard Contractual Clauses (SCCs). The BAA ensures compliance with HIPAA regulations when sharing PHI with vendors within the U.S., while SCCs (or equivalent mechanisms) are required under GDPR to legitimize cross-border data transfers. Each plays a specific role - HIPAA governs domestic compliance, while GDPR addresses international data transfer requirements.
What security controls best satisfy both HIPAA and GDPR for cross-border PHI?
When dealing with cross-border Protected Health Information (PHI), ensuring compliance with both HIPAA and GDPR is critical. Here are some of the most effective security measures to protect sensitive data:
- Encryption: Use AES-256 encryption for data at rest and TLS 1.2 or 1.3 for data in transit to safeguard information from unauthorized access.
- Strict Access Controls: Limit data access to only those who absolutely need it, following the principle of least privilege.
- Multi-Factor Authentication (MFA): Add an extra layer of security by requiring multiple forms of verification for system access.
On the legal side, several safeguards help maintain compliance:
- Standard Contractual Clauses (SCCs) and Binding Corporate Rules (BCRs): These legal frameworks ensure proper handling of personal data during international transfers.
- Business Associate Agreements (BAAs): These contracts outline responsibilities and compliance requirements between covered entities and their partners.
Finally, ongoing evaluations are key. Continuous risk assessments, including Transfer Impact Assessments (TIAs), help identify and mitigate risks associated with international data transfers, ensuring both compliance and security.


