Telehealth Risk Assessment Frameworks
Post Summary
Telehealth is transforming healthcare delivery, but it comes with challenges like data breaches, phishing, and compliance issues. Effective risk assessment frameworks help protect patient data, meet regulations, and secure telehealth systems. Here's a quick overview of key strategies:
- Identify Assets: Catalog sensitive data, devices, and systems involved in telehealth.
- Assess Threats: Address risks like phishing, outdated software, and weak authentication.
- Ensure Compliance: Follow HIPAA rules for data security and privacy, including BAAs for vendors.
- Frameworks to Use:
- NIST Risk Management Framework (RMF): A structured, step-by-step process.
- Attack Tree Modeling: Visual maps of potential cyberattack scenarios.
- Integrated Security Framework: Combines asset value, attack probability, and risk scoring.
Tools like Censinet RiskOps™ simplify vendor assessments, automate workflows, and enable continuous monitoring. With telehealth encounters surging, adopting these practices can reduce vulnerabilities and protect patient trust.
Telehealth Data Privacy and Security: Strategies and Solutions for Providers
sbb-itb-535baee
Core Elements of Telehealth Risk Assessment
A thorough telehealth risk assessment boils down to three main tasks: understanding what needs protection, identifying potential threats, and ensuring compliance with applicable regulations. These steps create a strong foundation for healthcare organizations to navigate risks effectively before implementing specific controls.
Identifying and Categorizing Assets
Start by listing everything involved in delivering patient care through telehealth. This includes sensitive data like PHI (Protected Health Information) and medical records, as well as the systems, devices, and services that support care delivery.
- Enterprise systems: Think of clinical systems, telehealth platforms, and the IT infrastructure running behind the scenes.
- Third-party services: Cloud providers, integrated software, and vendors with system access play a big role in telehealth operations.
- Connected devices: Medical devices and Internet of Medical Things (IoMT) equipment used for remote monitoring directly impact patient safety and must be carefully tracked.
Categorizing these assets means looking at two factors: how sensitive the data is and how critical it is to patient outcomes. A dynamic approach, like RiskOps, helps keep this inventory updated as assets and risks evolve.
Ed Gaudet, CEO of Censinet, aptly states: "The Risk Never Sleeps Podcast highlights the people protecting patient safety in today's fast-paced, high-demand, increasingly digital healthcare environment" [1].
With your assets mapped out, the next step is to assess the threats and vulnerabilities that could affect them.
Threat and Vulnerability Assessment
Once you know what you're protecting, it’s time to pinpoint what could go wrong. Telehealth faces a range of risks, including phishing attacks, unauthorized access to video sessions, and data breaches. These risks can be grouped into three areas:
- Policies: Authentication protocols and consent processes must be airtight.
- Technology: Data protection measures like encryption and access controls are key.
- Training: Both staff and patients need to understand and follow security practices [2].
Vulnerabilities can be surprisingly common. Issues like unencrypted connections, outdated software, or lack of privacy during virtual visits create opportunities for attackers. Even clinician home networks and mobile devices can expand the attack surface. To mitigate these risks:
- Use encryption, firewalls, and updated antivirus software to secure connections.
- Verify patient identity before starting any session.
- Conduct visits in private, enclosed spaces to prevent eavesdropping.
- For follow-ups, rely on encrypted messaging or secure patient portals instead of standard email or text.
Clear processes and solid technical defenses go a long way in reducing threats. Once threats are assessed, it’s crucial to align with regulatory requirements.
Regulatory and Compliance Requirements
Federal and state laws heavily influence telehealth risk assessments. For example:
- The HIPAA Privacy Rule (45 CFR Parts 160 and 164, Subparts A and E) governs who can access or disclose PHI.
- The HIPAA Security Rule (45 CFR Part 164, Subparts A and C) outlines safeguards for electronic PHI (ePHI), including visit recordings and biometric data.
A formal risk analysis is essential to identify where ePHI is created, stored, or transmitted - whether on clinician home networks or mobile devices. Any third-party vendor handling patient data must sign a Business Associate Agreement (BAA).
As the National Telehealth Authority puts it: "A platform that refuses to sign one [BAA] - regardless of how polished its interface looks - is not compliant to use for patient care" [3].
Clinicians working across state lines must also adhere to state laws, which may impose stricter privacy rules than federal HIPAA standards, especially for sensitive data like mental health records. Risk analyses aren’t a one-and-done task - they need regular updates as new technologies and threats arise. Administrative audits should track who accessed specific records and when.
| Compliance Element | Regulatory Basis | Telehealth Application |
|---|---|---|
| Risk Analysis | HIPAA Security Rule | Documenting ePHI flow across home networks and vendor data centers |
| Technical Safeguards | HIPAA Security Rule | Encryption in transit/at rest, MFA, and session timeouts |
| Business Associates | HIPAA Privacy/Security Rules | Mandatory contracts (BAAs) for all software and cloud vendors |
| Notice of Privacy Practices | HIPAA Privacy Rule | Providing and documenting electronic delivery of privacy policies |
| State Law Compliance | Various State Statutes | Adhering to stricter-than-federal rules in multi-state practices |
Common Risk Assessment Frameworks for Telehealth
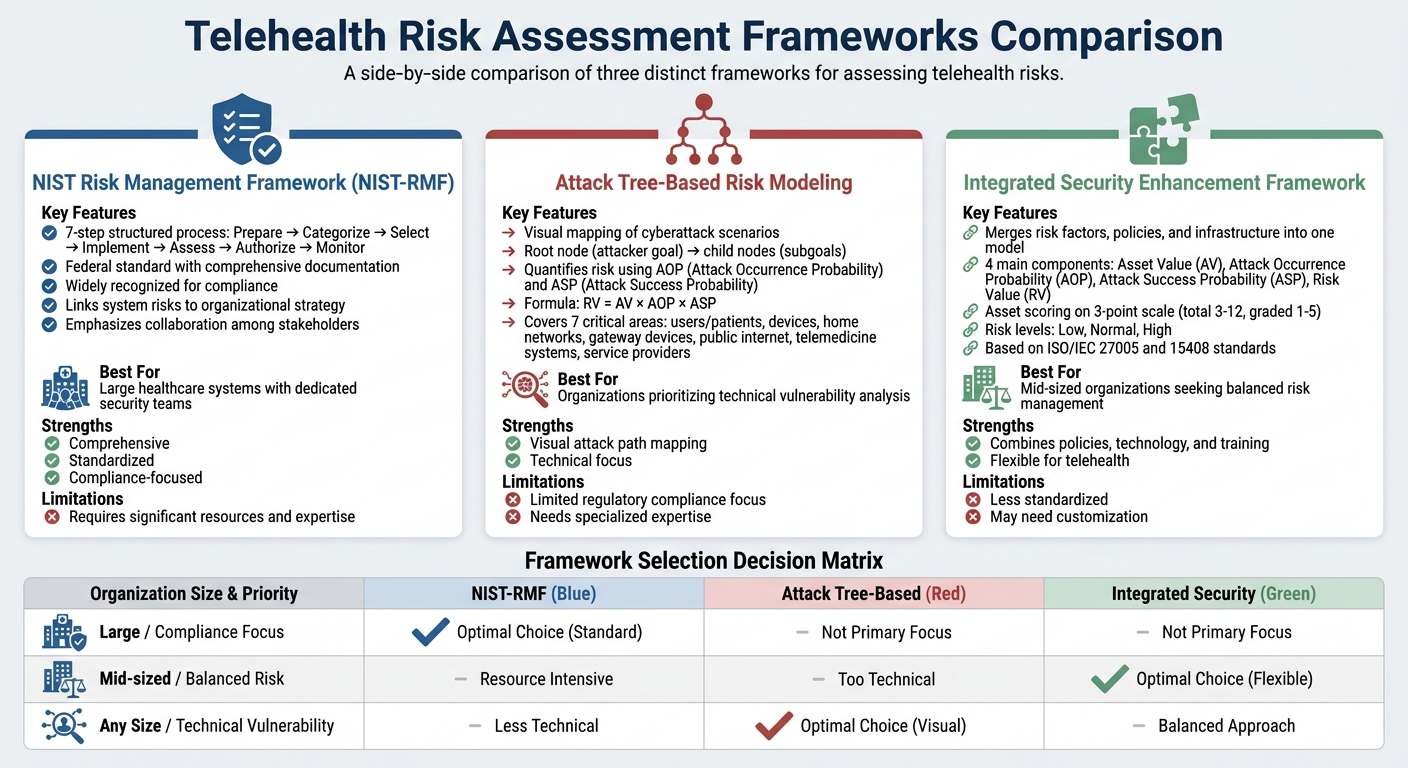
Telehealth Risk Assessment Frameworks Comparison: NIST-RMF vs Attack Tree vs Integrated Security
Once you've mapped out your assets and compliance requirements, the next step is to choose a framework that aligns with your telehealth setup. These frameworks are designed to help you systematically evaluate and manage risks. Some focus on step-by-step processes, others rely on visual tools, and some use scoring systems to quantify risks. The best fit depends on your organization's needs, available resources, and the specific telehealth services you provide.
NIST Risk Management Framework (NIST-RMF)
The NIST Risk Management Framework provides a structured, seven-step process tailored for managing risks in systems like telehealth platforms. These steps - Prepare, Categorize, Select, Implement, Assess, Authorize, and Monitor - help healthcare organizations integrate risk management into their operations [6].
"The Risk Management Framework (RMF) from NIST provides a structured yet flexible process for managing risk throughout a system's life cycle." - CMS Information Security and Privacy Program [6]
What makes NIST-RMF stand out is its ability to link specific system risks - such as vulnerabilities in a Remote Patient Monitoring (RPM) app - to the organization's overall risk strategy [6]. This framework emphasizes collaboration among all telehealth stakeholders, including Healthcare Delivery Organizations (HDOs), platform providers, and patients, ensuring that each party addresses risks within their scope [4][5].
For example, during the "Select" phase, you can apply security controls tailored to RPM systems, which often involve data transfers between patient homes, healthcare providers, and telehealth platforms. The "Monitor" phase ensures ongoing vigilance, which is crucial in dynamic telehealth environments where external devices are part of the ecosystem [6].
NIST-RMF also stresses the importance of balancing people, processes, and technology. It assigns clear accountability for security measures, including those inherited from third-party services like cloud providers used by telehealth platforms [6].
| RMF Step | Telehealth Application Example |
|---|---|
| Prepare | Identifying all actors in the RPM ecosystem, such as HDOs and platform providers [4][6]. |
| Categorize | Evaluating the impact of a breach involving sensitive patient health information (PHI) [6]. |
| Select | Implementing encryption and access controls for remote monitoring devices [4][6]. |
| Implement | Deploying multi-factor authentication and zero trust architecture [4][6]. |
| Assess | Testing if data transmission from patient devices is securely encrypted [6]. |
| Authorize | Gaining approval for telehealth system operation based on risk assessments [6]. |
| Monitor | Using analytics to detect unauthorized access to patient data in real time [4][6]. |
Next, we'll look at how attack tree modeling provides a visual alternative to risk assessment.
Attack Tree-Based Risk Modeling
Attack trees offer a visual way to map out potential cyberattack scenarios, starting with an attacker’s ultimate goal (root node) and branching into subgoals (child nodes) [7]. This method is particularly effective for telehealth because it shifts the focus to understanding how attackers might exploit vulnerabilities.
"Identifying all possible defined attacks facilitates analysis of all possible cyberattack access paths and selection of the best-suited countermeasures and their optimal deployment." - BMC Medical Informatics and Decision Making [7]
Attack trees quantify risk using two key metrics: Attack Occurrence Probability (AOP) and Attack Success Probability (ASP). ASP is calculated based on factors like time needed to exploit a vulnerability, required expertise, system knowledge, access opportunities, and necessary tools [7]. Combining these metrics with Asset Value (AV) gives a Risk Value (RV):
RV = AV × AOP × ASP [7].
This approach helps prioritize which telehealth components need immediate attention. For instance, attack trees can be applied to seven critical areas: users/patients, devices, home networks, gateway devices, public internet, telemedicine systems, and service providers [7].
A real-world example highlights the importance of this framework. In 2013, former U.S. Vice President Dick Cheney's medical team disabled the Wi-Fi function of his implantable cardioverter-defibrillator (ICD) to prevent potential hacking - a scenario often modeled in healthcare attack trees to demonstrate the risks of implantable medical device (IMD) vulnerabilities [7].
When building attack trees, red teams (simulating attackers) create the models, while blue teams (defenders) develop countermeasures based on the findings [7]. Special attention should be given to the "User/Patient" area, as many telehealth users lack cybersecurity training and may inadvertently expose systems to risks like phishing or device theft [7].
For organizations seeking a consolidated approach, integrated frameworks offer another option.
Integrated Security Enhancement Framework
The Integrated Security Enhancement Framework merges various risk factors, organizational policies, and system infrastructure into one quantitative model [7]. It builds on four main components: Asset Value (AV), Attack Occurrence Probability (AOP), Attack Success Probability (ASP), and the resulting Risk Value (RV).
Asset Value is calculated by scoring confidentiality, integrity, availability, and the asset's overall contribution on a three-point scale. Scores are totaled (ranging from 3 to 12) and assigned an importance grade from 1 to 5 [7]. Attack trees are then used to map potential attack paths, and the framework determines AOP by analyzing the number of events required to achieve a goal [7].
Risk values are categorized into three levels: low, normal, and high [7]. For example, in one case study involving patient data leakage, an AOP of 6.25% was calculated based on the complexity of the attack path [7]. This framework is especially relevant for remote medical services, which have grown in importance due to events like the COVID-19 pandemic [7].
Using ISO/IEC 27005 and 15408 standards, the framework identifies threats and evaluates attack potential [7]. To apply it in telehealth, start by categorizing assets (e.g., IMDs, servers, gateways) and assigning values based on the potential impact of a breach. Consider the "window of opportunity" as well - devices in patient homes often have longer exposure periods than those in clinical settings. The Risk Value helps determine which areas need immediate security measures and which are already secure [7].
Cloud Security in Telehealth Risk Management
Telehealth platforms rely heavily on cloud infrastructure for storing patient data and enabling remote access. While this setup offers convenience, it also introduces significant security challenges. In 2023, 94% of healthcare organizations reported data breaches in cloud environments, with each breach costing an average of $10.1 million [17]. Telehealth platforms have been particularly vulnerable, experiencing a 300% surge in cyberattacks between 2020 and 2023 [18]. These statistics highlight how crucial cloud security is within telehealth risk management.
Data Classification and Access Controls
Properly classifying data and implementing strict access controls are essential to reducing vulnerabilities in cloud environments. Using guidelines like NIST 800-60, healthcare organizations can label data based on sensitivity - categories include public, internal, confidential, and restricted. For telehealth, sensitive data such as patient video consultations and e-prescriptions are classified as restricted and must be encrypted both at rest and during transmission [8].
Access controls ensure that only authorized individuals can interact with sensitive data. Role-Based Access Control (RBAC) assigns permissions based on job roles - doctors, for instance, can access full patient records, while receptionists are limited to scheduling information. Attribute-Based Access Control (ABAC) takes this further by adding dynamic factors like device trust or user location, reducing the risk of breaches from unverified devices. Studies show that ABAC can lower breach risks by 40% [9]. Tools like AWS IAM help enforce these policies, ensuring only approved devices and users can access protected health information (PHI).
Automation can further enhance security. For example, AWS Macie scans and tags sensitive data automatically, while multi-factor authentication (MFA) and least-privilege principles add extra layers of protection. Temporary permissions, such as just-in-time access, limit exposure by granting access only when absolutely necessary [14].
Zero Trust Architecture and Vulnerability Management
A Zero Trust Architecture operates on the principle of "never trust, always verify." Even familiar networks must verify every access request, whether it’s for video consultations or electronic health record (EHR) retrievals [15]. This approach integrates seamlessly with broader telehealth security frameworks. Guidance from NIST SP 800-207 emphasizes continuous authentication and micro-segmentation, which isolates data silos to limit damage during breaches [10].
Vulnerability management complements Zero Trust by focusing on proactive scanning and patching. Tools like Qualys perform daily scans of cloud APIs and virtual endpoints, targeting vulnerabilities that could be exploited. Best practices include addressing zero-day vulnerabilities within 24 hours and conducting quarterly penetration tests, which can reduce exploit risks by 70% [11]. Cloud-native tools such as AWS GuardDuty and Azure Sentinel offer real-time threat detection, flagging suspicious activity before it escalates into a full-blown breach.
Third-Party Risk Assessments
Third-party vendors - such as cloud providers, SaaS teleconferencing platforms, and remote monitoring device manufacturers - introduce additional risks to telehealth systems. Reports from 2024 reveal that 60% of healthcare data breaches involve third-party vendors [12]. These vendors can create vulnerabilities through shared responsibility gaps, data leaks, and supply chain issues.
To mitigate these risks, healthcare organizations should conduct effective third-party risk assessments. Key considerations include SOC 2 compliance, data residency requirements, and service-level agreements (SLAs) that align with HIPAA standards. Frameworks like the SIG Questionnaire help assess how vendors handle PHI, their incident response plans, and their overall cybersecurity practices [16].
Automated platforms like Censinet RiskOps™ simplify vendor risk management by automating assessments, scoring risks, and enabling real-time collaboration. These platforms also benchmark vendor security against industry peers and continuously monitor cloud vendors’ cybersecurity measures - especially for telehealth integrations involving remote monitoring devices and virtual care platforms.
| Cloud Security Practice | Key Telehealth Application | Recommended Tools/Frameworks |
|---|---|---|
| Data Classification | PHI categorization | NIST 800-60, AWS Macie |
| Access Controls | Remote clinician access | MFA, RBAC, Okta |
| Zero Trust | Continuous verification | Zscaler, NIST SP 800-207 |
| Vulnerability Management | Patch telehealth apps | Qualys, Cloud CWPP |
| Third-Party Risk | Vendor cloud audits | Censinet RiskOps™, SIG |
Tracking metrics like mean time to detect and fix vulnerabilities (target under 48 hours), third-party compliance scores (target above 80%), and access denial rates for unauthorized attempts (target above 95%) can help organizations measure and improve their telehealth cloud security over time [13].
Using Censinet RiskOps™ for Telehealth Risk Management

Censinet RiskOps™ simplifies telehealth risk management by offering a platform tailored to the unique challenges faced by healthcare delivery organizations. From managing sensitive patient data within cloud-based telehealth systems to assessing third-party vendors for video conferencing, remote monitoring devices, and EHR integrations, this platform addresses critical needs. Below, we explore how Censinet RiskOps™ improves third-party assessments, leverages automation, and promotes collaborative, real-time monitoring.
Streamlined Third-Party and Enterprise Risk Assessments
Telehealth organizations often juggle multiple vendors, including cloud service providers, communication platforms, medical device manufacturers, and SaaS solutions. Evaluating the security and compliance of these vendors manually can drag on for weeks, requiring coordination across IT, compliance, and clinical teams. Censinet RiskOps™ simplifies this process by offering standardized frameworks that reduce manual work while providing comprehensive oversight of the telehealth ecosystem.
The platform allows organizations to systematically evaluate vendor security measures, compliance levels, and risk profiles. Pre-built frameworks aligned with HIPAA, HITECH, and the NIST Cybersecurity Framework ensure consistent evaluation criteria across all third parties. This approach not only makes it easier to identify high-risk vendors but also helps prioritize remediation efforts based on their potential impact on patient safety and data security. By centralizing and standardizing assessments, healthcare organizations can maintain regulatory alignment and focus on continuous risk monitoring.
AI-Powered Automation with Censinet AI™

Taking assessments to the next level, Censinet AI™ introduces automation to speed up the process. Tasks that traditionally take weeks - like evidence validation, data collection, and reporting - can now be completed in days. The AI swiftly analyzes vendor responses, identifies patterns, and generates concise reports while ensuring consistent evaluation criteria across all vendors.
For example, the AI can flag critical issues such as missing encryption protocols or inadequate incident response plans, ensuring these are immediately prioritized by security teams. Vendors also benefit, as they can complete security questionnaires in seconds, with the AI summarizing their evidence and generating risk reports based on the assessment data. This automation not only accelerates the process but also ensures thorough oversight through configurable rules and review mechanisms.
Collaborative Risk Management and Continuous Monitoring
Managing telehealth risks effectively requires collaboration among various stakeholders, including clinical teams, IT security, compliance officers, and vendor representatives. Censinet RiskOps™ brings these groups together by centralizing assessment findings and enabling them to work collectively on mitigation strategies, assign tasks, and monitor progress toward resolving issues. This collaborative approach ensures that both technical and operational risks are addressed.
The platform also shifts from annual assessments to continuous monitoring, providing real-time insights into vendor security postures, compliance updates, and emerging vulnerabilities. Alerts are automatically sent when a vendor’s risk profile changes, such as when a telehealth platform reports a new vulnerability or loses a security certification. With real-time alerts and collaborative dashboards, stakeholders can respond quickly to threats. Additionally, the platform offers detailed reporting features, including risk scoring trends, vendor comparisons, remediation tracking, and executive-level dashboards. These tools help communicate systematic risk management efforts to leadership, boards, and regulators effectively.
Implementation Steps and Best Practices
Turning risk assessment principles into action requires a structured approach. To implement a telehealth risk assessment framework effectively, start by identifying and categorizing all assets. This includes third-party IT services, billing systems, cloud storage solutions, and telehealth platforms - key areas where security and compliance risks are concentrated. Align these risk scores with the sensitivity of the assets and the potential threats they face.
Begin by cataloging assets and identifying security gaps. Evaluate vendors for their ability to handle PHI (Protected Health Information) and their compliance with HIPAA standards. Use a weighted scoring system (e.g., a scale of 100) to calculate risk scores, prioritizing factors like full access to PHI. Next, verify vendor security credentials by reviewing certifications, service types, and operational reliability. Finally, implement mitigation strategies - this could mean asking for additional certifications, revising contracts, or increasing monitoring for higher-risk vendors.
Step-by-Step Implementation Guide
The process unfolds across three key phases:
- Pre-visit phase: Secure informed consent, verify that data transmissions are encrypted, and audit physical spaces for privacy and proper lighting.
- During-visit phase: Confirm patient identity using government-issued ID, ensure internet connections are encrypted, avoid unnecessary recordings, and secure all devices with strong passwords.
- Post-visit phase: Use encrypted communication portals for follow-ups and gather feedback from patients and staff to assess comfort with the security measures in place.
Risk analysis shouldn’t be a one-and-done task. Regular reviews are essential to address new threats as they arise. Move beyond generic checklists by using healthcare-specific insights to identify precise vulnerabilities. While automated tools can provide a solid starting point, major decisions should always involve your internal compliance team.
After defining these phases, compare different frameworks to find the one that aligns best with your telehealth setup.
Framework Comparison for Telehealth
Choosing the right framework depends on your organization's needs, resources, and regulatory obligations. Here’s a quick comparison to guide your decision:
| Framework | Primary Strengths | Key Limitations | Best Suited For |
|---|---|---|---|
| NIST Risk Management Framework (NIST-RMF) | Federal standard with comprehensive documentation; widely recognized for compliance | Requires significant resources and expertise | Large healthcare systems with dedicated security teams |
| Attack Tree-Based Risk Modeling | Maps specific attack paths; great for technical teams | Limited focus on regulatory compliance; needs specialized expertise | Organizations prioritizing technical vulnerability analysis |
| Integrated Security Enhancement Framework | Combines policies, technology, and training; flexible for telehealth | Less standardized and may need customization | Mid-sized organizations seeking balanced risk management |
When evaluating frameworks, think about your organization’s security maturity, available resources, and the complexity of your telehealth operations. Frameworks that emphasize vendor accountability are particularly effective for safeguarding patient trust and reducing the risk of security breaches.
Once you’ve selected a framework, technology integrations can take your risk management efforts to the next level.
Integrating Technology Solutions Like Censinet Connect™
Platforms like Censinet Connect™ simplify and standardize risk assessments, saving time and improving data security. These tools automate vendor evaluations, ensuring a consistent and thorough process across all vendors. By streamlining workflows, they eliminate the gaps often found in manual assessments.
Integrating these tools with existing systems creates a central hub for managing telehealth risks, from cloud providers to remote patient monitoring devices. Combining standardized frameworks, automated scoring, and continuous monitoring builds a scalable risk management strategy. Additionally, organizations should establish incident response plans, complete with communication protocols and data backup strategies, to address potential privacy breaches or security incidents efficiently. Technology solutions play a vital role in enabling rapid and effective responses to such challenges.
Conclusion
Telehealth is reshaping how care is delivered, but it also brings a host of security challenges that demand vigilant risk management. The frameworks discussed here - NIST Risk Management Framework, Attack Tree-Based Risk Modeling, and the Integrated Security Enhancement Framework - provide practical strategies for identifying critical assets, assessing potential threats, and staying compliant with regulations like HIPAA.
Modern tools are stepping in to make risk management more efficient. For instance, Censinet RiskOps™ simplifies third-party and enterprise risk assessments, automates workflows with Censinet AI™, and enables ongoing monitoring of PHI, medical devices, and supply chains. Organizations using Censinet RiskOps™ report cutting vendor assessment times by up to 70%, freeing up security teams to focus on higher-priority tasks.
"By 2027, 90% of telehealth breaches will stem from third-party risks - AI-driven platforms like Censinet AI™ are non-negotiable." - Gartner's 2025 forecast
The benefits of combining structured frameworks with advanced tools are clear. One U.S. health system that implemented NIST-RMF alongside third-party risk tools during a 2024 ransomware surge reduced supply chain security challenges by 45%, maintained 99.9% uptime for telehealth services, and avoided nearly $5 million in potential fines. These results highlight how a proactive approach can lead to stronger, more scalable security measures.
To enhance your telehealth security, start by creating a complete inventory of your assets. Test a framework that aligns with your organization's needs, conduct quarterly third-party audits, evaluate if your third-party risk assessments are truly effective, integrate Zero Trust architecture principles, and schedule annual reviews of your framework. With telehealth encounters in the U.S. expected to hit 1 billion annually by 2025 and frameworks capable of reducing vulnerabilities by up to 60%, acting now is crucial. According to Forrester's 2024 research, proactive measures can cut breach risks by 50%, protecting both patient data and your organization's reputation and financial health. By adopting these strategies, you can build a resilient security program that keeps pace with evolving threats.
FAQs
Which telehealth risk assessment framework should I start with?
A helpful resource to begin with is the Checklist for Evaluating Telehealth Security Maturity by Censinet. This checklist dives into key areas like governance, technical safeguards, vendor management, and workforce training. It’s designed to assist organizations in strengthening their overall security measures.
When addressing third-party risks, the Telehealth Vendor Risk Management framework is invaluable. It emphasizes vendor assessments, along with considerations for security, privacy, and clinical safety. By combining these two frameworks, organizations can tackle telehealth risk management from multiple angles, ensuring no critical aspect is overlooked.
What telehealth assets should be included in a risk assessment?
When conducting a telehealth risk assessment, it's crucial to examine the key components that ensure secure and effective service delivery. This includes evaluating hardware, software, connected devices, and the platforms used in telehealth operations.
Don't overlook third-party vendors, cloud services, and medical devices used for remote monitoring. Communication tools like encrypted messaging and video conferencing platforms should also be part of the assessment.
Key areas to focus on include:
- Security controls: Check for measures like encryption and multi-factor authentication to protect sensitive data.
- Regulatory compliance: Ensure vendors meet standards such as HIPAA to maintain legal and ethical standards.
- Workforce policies: Review training programs for employees to make sure they understand security protocols.
- Continuous monitoring: Implement systems to regularly track and address potential risks, ensuring ongoing patient safety.
By covering these elements, you can create a safer and more reliable telehealth environment.
How often should telehealth risk assessments and vendor reviews be updated?
Telehealth risk assessments and vendor reviews should be revisited at least once a year or whenever major changes take place. These regular updates are key to staying compliant and spotting new risks, which helps safeguard the security and dependability of telehealth systems.


