GDPR vs. HIPAA: Consent Management Differences
Post Summary
GDPR and HIPAA manage health data differently, creating challenges for global healthcare organizations. GDPR, applicable worldwide for EU data, requires explicit consent for processing health information. HIPAA, a U.S. law, allows the use of Protected Health Information (PHI) for treatment, payment, and operations without prior consent but requires written authorization for non-routine uses like marketing or data sales.
Key Points:
- GDPR: Explicit opt-in consent is mandatory for health data unless specific exemptions apply. Patients can withdraw consent easily and have a "Right to Be Forgotten."
- HIPAA: Consent isn’t required for routine uses (Treatment, Payment, Operations). Non-routine uses need detailed written authorization.
- Penalties: GDPR fines can reach €20 million or 4% of global turnover, while HIPAA violations can cost up to $1.9 million per violation annually.
- Scope: GDPR applies globally to EU residents' data, while HIPAA is U.S.-focused.
Quick Comparison:
| Feature | GDPR | HIPAA |
|---|---|---|
| Consent Requirement | Explicit opt-in for health data | Not required for routine uses (TPO) |
| Non-Routine Uses | Needs explicit consent or exemptions | Requires written authorization |
| Right to Erasure | Yes | No |
| Jurisdiction | Global (EU residents' data) | U.S. only |
| Breach Notification | 72 hours | 60 days to avoid data breach penalties |
| Maximum Penalties | €20M or 4% of global turnover | $1.9M per violation category annually |
How to Comply: Use strict GDPR standards for EU patients and HIPAA rules for U.S. operations. Tailor consent processes regionally, manage third-party vendor risk with dual agreements, and leverage technology to streamline compliance.
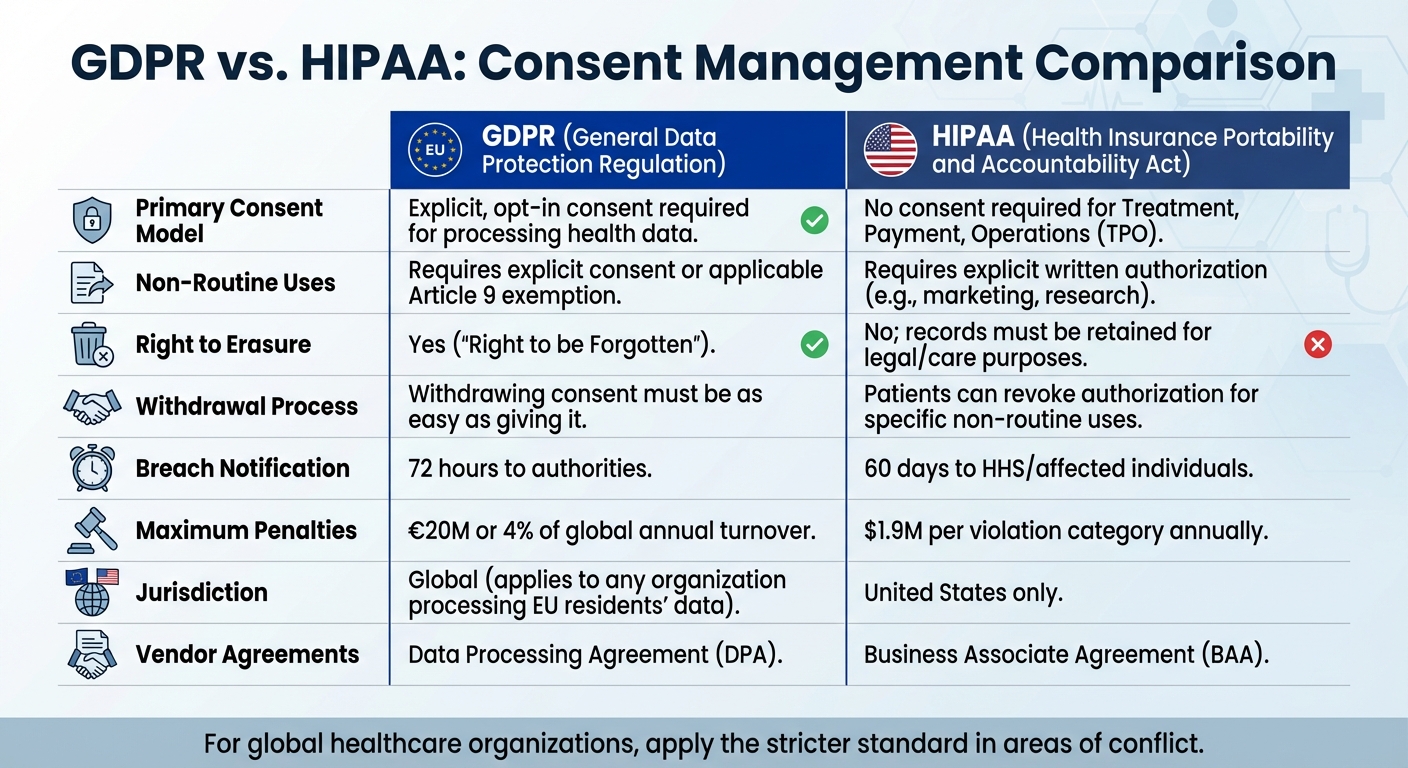
GDPR vs HIPAA Consent Management Comparison Chart
Data Protection in the US vs in the EU - GDPR vs HIPAA
sbb-itb-535baee
GDPR Consent Requirements
Under GDPR, health data is classified as a special category that demands explicit consent - a stricter standard than the "unambiguous" consent required for standard personal data. For health information, implied agreement or inferred permission isn’t enough. Consent must be a clear and affirmative statement that explicitly identifies the sensitive data being processed.
To comply, consent must be freely given, specific to each purpose, informed, and unambiguous.
"Consent should not be regarded as freely given if the data subject has no genuine or free choice or is unable to refuse or withdraw consent without detriment." - GDPR Recital 42 [5]
Equally important is the right to withdraw consent. Patients can revoke their permission at any time, and the process for doing so must be as simple as granting consent. Healthcare organizations must also maintain verifiable records to prove that proper consent was obtained.
Explicit and Informed Consent
When it comes to health data, the "explicit" consent requirement leaves no room for vague or generalized agreements. Many health apps in the EU rely on user consent for processing, but regulators are paying close attention. For instance, French authorities fined Google €50 million after determining that information about data processing for ad personalization was scattered across multiple documents, making it difficult for users to fully understand [5]. Similarly, the British Information Commissioner’s Office states: "If the request for consent is vague, sweeping or difficult to understand, then it will be invalid" [5].
Transparency is essential at every stage. Patients must be informed about the identity of the data controller, the specific purposes for processing, the types of data being collected, and their right to withdraw consent. In 2024, the Italian Garante fined a health app €1.5 million for bundling health data consent with marketing consent, violating these principles [6]. Likewise, Ireland’s Data Protection Commission fined Meta €390 million in January 2023 for using "contractual necessity" as a workaround instead of obtaining explicit consent for behavioral advertising [7].
To ensure compliance, healthcare organizations should adopt two-step confirmation processes. This could include an initial screen for granular preferences, followed by a summary screen for final confirmation. Each consent purpose - whether for health data, marketing, or general terms - must have its own distinct checkbox. Bundling these together is a clear violation. Additionally, organizations must keep detailed records of every consent instance to demonstrate compliance if questioned.
When explicit consent isn’t feasible, GDPR outlines alternative legal bases for processing health data.
Legal Bases for Data Processing
For global organizations, knowing when explicit consent isn’t required is critical. GDPR allows health data processing without consent in situations where delays could compromise care. Article 9 provides exceptions for specific circumstances.
Healthcare provision is one of the most common exceptions. Licensed healthcare providers can process patient data for purposes like diagnosis, treatment, or healthcare system management, as long as the data is handled by professionals bound by confidentiality. However, this exception generally doesn’t extend to consumer health apps or commercial wellness platforms.
Vital interests apply in emergencies where processing is necessary to protect someone’s life, especially if they’re unable to provide consent. Public health exceptions cover activities like disease surveillance, epidemic response, or ensuring healthcare quality and safety standards. Scientific research is also permitted under Article 89, provided safeguards like pseudonymization and ethics approval are in place.
A case from 2024 highlights the risks of non-compliance. Sweden’s Data Protection Authority fined a healthcare provider €12 million for processing patient data without proper consent and failing to apply an appropriate legal basis [6]. This underscores the importance of carefully evaluating which legal basis applies to each activity and maintaining thorough documentation to back up these decisions.
HIPAA Consent and Authorization Rules
HIPAA takes a different approach compared to GDPR's explicit consent model, allowing the routine use and disclosure of Protected Health Information (PHI) without requiring explicit consent. It separates this into two mechanisms: voluntary "consent" for routine healthcare activities and mandatory "authorization" for non-routine uses. Healthcare organizations must know when they can proceed without patient permission and when formal authorization is required. This distinction is key to understanding HIPAA's flexibility versus its stricter requirements.
Permitted Uses Without Consent
HIPAA permits covered entities to use or disclose PHI without explicit consent for Treatment, Payment, and Healthcare Operations (TPO). Here's what each category includes:
- Treatment: Activities like diagnosing, coordinating care, and making referrals.
- Payment: Handling billing, processing insurance claims, and managing collections.
- Healthcare Operations: Tasks such as quality improvement, staff training, and business planning.
"Healthcare providers have complete discretion to design a process that best suits their needs" regarding the collection of voluntary consent for TPO. - HHS [8]
Additionally, HIPAA allows the use or disclosure of PHI without authorization for certain national priority purposes, such as public health monitoring, law enforcement requests, judicial proceedings, and other legally mandated uses. Providers can also share information with family or friends involved in a patient’s care if the patient is present and does not object. Other permissible disclosures include providing PHI directly to the individual, using de-identified data, or sharing limited data sets under formal agreements [8][9].
Although HIPAA makes consent optional for TPO, many healthcare organizations voluntarily implement consent processes to foster patient trust and comply with stricter state-level regulations.
Authorization for Non-Routine Uses
For uses beyond TPO, a valid written authorization is required. This document must include specific details to be legally valid.
Authorization is necessary for activities such as:
- Marketing communications, especially those involving financial compensation from third parties.
- Sale of PHI.
- Disclosure of psychotherapy notes.
- Most research purposes that don’t qualify for an IRB waiver.
- Sharing PHI with third parties, like employers for fitness evaluations or insurers for underwriting.
- Social media posts featuring patient information or images.
"Where the Privacy Rule requires patient authorization, voluntary consent is not sufficient to permit a use or disclosure of protected health information unless it also satisfies the requirements of a valid authorization." - HHS [8]
A valid authorization must specify the PHI being disclosed, the parties involved, the purpose, expiration date, revocation rights, and include a disclosure warning along with the patient’s dated signature [8][9]. Missing any of these elements invalidates the authorization. Unlike general consent, healthcare providers cannot condition treatment on a patient signing an authorization for non-routine uses. Patients can also revoke their authorization in writing at any time, though this does not apply to information already disclosed [8][9].
Key Differences Between GDPR and HIPAA in Consent Management
Building on the distinct consent models discussed earlier, let's dive into the key differences that impact global healthcare organizations.
Under GDPR, explicit opt-in consent is required for processing special category health data. In contrast, HIPAA permits the use of Protected Health Information (PHI) for Treatment, Payment, and Operations (TPO) without prior consent.
Another major distinction lies in their scope. GDPR applies globally to any organization handling the data of EU residents, while HIPAA is restricted to entities operating within the United States.
"The answer to GDPR vs HIPAA is not to choose one. It's to build a compliance programme that satisfies both - starting with the stricter standard in each area of conflict." – Custodia
GDPR also offers EU residents a "Right to Be Forgotten" and a straightforward consent withdrawal process. HIPAA, however, mandates the retention of medical records per state laws and does not provide a right to erasure.
Comparison Table: GDPR vs. HIPAA Consent Management
Here’s a quick look at how GDPR and HIPAA differ in consent management:
| Feature | GDPR | HIPAA |
|---|---|---|
| Primary Consent Model | Explicit, opt-in consent is required for processing health data | No consent required for Treatment, Payment, or Operations (TPO) |
| Non-Routine Uses | Requires explicit consent or an applicable Article 9 exemption | Requires explicit written authorization (e.g., for marketing or research) |
| Right to Erasure | Yes ("Right to be Forgotten") | No; records must be retained for legal or care purposes |
| Withdrawal Process | Withdrawing consent must be as easy as giving it | Patients can revoke authorization for specific non‐routine uses |
| Breach Notification | Notification to authorities within 72 hours | Notification to HHS or affected individuals within 60 days |
| Maximum Penalties | Up to €20 million or 4% of global annual turnover | Up to $1.9 million per violation category per year |
| Jurisdiction | Global – applies to any organization processing data of EU residents | United States only |
| Vendor Agreements | Requires a Data Processing Agreement (DPA) | Requires a Business Associate Agreement (BAA) |
These differences highlight the need for tailored compliance strategies.
What This Means for Global Healthcare Organizations
For healthcare organizations operating across both jurisdictions, understanding these distinctions is crucial for creating dual-compliance strategies.
Being HIPAA-compliant doesn’t automatically ensure GDPR compliance. For instance, GDPR's strict consent requirements, the need for a Data Protection Officer, and rules for international data transfers demand additional measures. Applying HIPAA’s TPO exceptions to EU patients won’t meet GDPR’s higher threshold for explicit consent.
To navigate these challenges, organizations should follow the strictest standards in areas of conflict. For example, adopting GDPR's 72-hour breach notification timeline alongside HIPAA's strong security safeguards can help ensure compliance with both frameworks.
Consent flows should also be tailored by region. EU-based patients require explicit, granular opt-in consent to meet GDPR Article 9 requirements, while U.S. operations can rely on HIPAA’s TPO exceptions. This often involves maintaining separate documentation, consent forms, and processing records for different patient groups. This complexity extends to third-party risk management when sharing data with external partners.
Vendor management is another complex area. Organizations frequently need both Business Associate Agreements for HIPAA compliance and Data Processing Agreements for GDPR compliance, even when working with the same vendors. Platforms like Microsoft Azure and Salesforce Health Cloud offer specialized solutions with privacy controls that align with both GDPR and HIPAA requirements.
Finally, when handling erasure requests from EU residents, organizations must conduct a legal review to determine if HIPAA or state-level record retention laws override the GDPR request. Documenting such conflicts and invoking GDPR’s "legal obligation" exception can help justify continued data storage when U.S. laws mandate retention.
How to Achieve Compliance with Both Regulations
Ensuring compliance with both GDPR and HIPAA is no small feat. It requires a combination of advanced tools, clear processes, and always adhering to the stricter standard when the two regulations conflict.
Start by mapping your data flows. This means documenting all categories of health data, their origins, destinations, and the geographies of the users involved. This process helps you identify where GDPR’s explicit consent rules apply and where HIPAA’s TPO (Treatment, Payment, and Operations) exceptions are sufficient [1].
Next, implement segmented consent flows. For EU users, establish explicit, detailed consent mechanisms while documenting the legal basis for processing based on user location [1]. Your consent forms and data collection methods should vary depending on whether the data pertains to U.S. or EU patients. However, all these processes should be managed within a unified system to maintain consistency and control.
Using Technology for Consent Management
Technology can make managing compliance across jurisdictions much simpler. Centralized consent management systems allow you to track GDPR’s strict opt-in requirements alongside HIPAA’s authorization rules for non-routine data uses [2].
Platforms like Censinet RiskOps™ are designed to support healthcare organizations in navigating these challenges. They automate risk assessments and manage third-party risks, handling tasks like GDPR’s Data Protection Impact Assessments (DPIAs) and HIPAA’s routine security risk analyses [3][4]. These platforms also maintain detailed logs and audit trails, creating a "single source of truth" for regulatory reporting and inspections [3][4].
Advanced systems can also enforce the stricter compliance standard automatically. For instance, you can configure your breach notification process to meet GDPR’s 72-hour requirement, which also satisfies HIPAA’s 60-day rule. Similarly, encryption proof used for HIPAA’s Security Rule can cover GDPR’s Article 32 requirements [3].
For vendor management, these tools automate onboarding and evidence analysis, ensuring that both Business Associates (under HIPAA) and data processors (under GDPR) follow compliant data-handling protocols [3][4]. This dual functionality is particularly useful when working with vendors who need both Business Associate Agreements (BAAs) and Data Processing Agreements (DPAs).
While technology plays a crucial role, internal best practices are equally important for achieving compliance.
Best Practices for Dual Compliance
Automated tools can handle much of the heavy lifting, but strong internal governance is essential. Start by assigning dual roles within your organization. Appoint a Data Protection Officer (DPO) for GDPR and a Privacy Officer for HIPAA. While these roles may overlap, each regulation has unique requirements that demand focused oversight [3][4].
Adopt universal data minimization practices. Both GDPR’s "data minimization" principle and HIPAA’s "minimum necessary" standard require collecting only the essential data needed for a specific purpose [1]. Making this your default approach ensures compliance with both regulations.
Use HIPAA’s detailed security measures, such as encryption, access controls, and audit logs, across your entire infrastructure. These safeguards not only meet HIPAA’s specific requirements but also address GDPR’s broader security expectations [1].
Automate compliance scanning to monitor patient-facing websites for tracking scripts or cookies that might collect data without consent. This is especially critical for GDPR, where consent must be obtained before any data collection begins [1].
Lastly, establish a dual-rights process for handling Data Subject Access Requests (DSARs). Both HIPAA and GDPR require these requests to be addressed within 30 days (or one month for GDPR). Create standardized workflows for data access, corrections, and permitted deletions to streamline this process [1].
Conclusion
GDPR and HIPAA take different approaches to consent and data handling. GDPR mandates explicit opt-in consent for processing health data unless a specific legal exception applies. In contrast, HIPAA allows the use and disclosure of Protected Health Information (PHI) for treatment, payment, and healthcare operations without prior consent.
To ensure compliance, organizations need clear consent processes and well-structured vendor agreements. This includes managing separate mechanisms for consent, establishing dual vendor contracts (such as Business Associate Agreements for HIPAA and Data Processing Agreements for GDPR), and addressing conflicting requirements like GDPR's right to erasure versus HIPAA's data retention rules. Non-compliance can lead to hefty fines: up to €20 million or 4% of global annual turnover under GDPR and civil penalties reaching approximately $1.9 million per violation category annually under HIPAA [1].
Meeting the stricter standard often simplifies dual compliance. For instance, adhering to GDPR's 72-hour breach notification rule also satisfies HIPAA's 60-day requirement [1]. Similarly, implementing strong technical safeguards can meet both frameworks' security demands. This approach not only ensures compliance but also reduces complexity across different jurisdictions.
Technology plays a critical role in managing these challenges. Tools like Censinet RiskOps™ help automate compliance tasks, from tracking legal bases for data processing to managing third-party risk assessments and maintaining detailed audit trails. By centralizing data, these platforms simplify reporting and inspections, making regulatory compliance more manageable.
For global healthcare organizations, achieving dual compliance is a must. With the right mix of advanced technology, strong internal governance, and a commitment to high standards, organizations can protect patient data effectively while staying aligned with both GDPR and HIPAA requirements, avoiding costly penalties in the process.
FAQs
When can EU health data be processed without consent under GDPR?
Under the General Data Protection Regulation (GDPR), health data in the EU can be processed without obtaining consent in specific situations. These include cases where processing is required to meet a legal obligation, serves public interest purposes, or is explicitly permitted by law. For instance, this might apply to public health initiatives or research projects, as long as there are sufficient safeguards to ensure the protection of such sensitive data.
What counts as a HIPAA “non-routine” use that needs authorization?
A HIPAA "non-routine" use requiring authorization refers to any use or disclosure of protected health information (PHI) that doesn't fit within the standard categories of treatment, payment, or healthcare operations (TPO). For instance, this could involve using PHI for marketing purposes or sharing it with third parties. Authorization is a critical step to ensure these actions align with HIPAA regulations and safeguard patient privacy.
How should global providers handle GDPR erasure requests vs. U.S. record retention?
Global providers face a tricky balancing act when dealing with GDPR erasure requests and U.S. record retention laws. Under GDPR, individuals have the right to request the deletion of their personal data unless there’s a valid reason to keep it, like meeting legal obligations. On the other hand, U.S. laws often require businesses to hold onto certain records for extended periods, which can sometimes take precedence over erasure requests.
To handle this overlap, providers should carefully document the legal grounds for retaining data. It’s also important to create clear, well-defined policies that aim to meet the requirements of both regulations whenever possible. This approach helps manage these conflicting obligations while staying compliant on both fronts.


