FDA Encryption Standards for Medical Devices
Post Summary
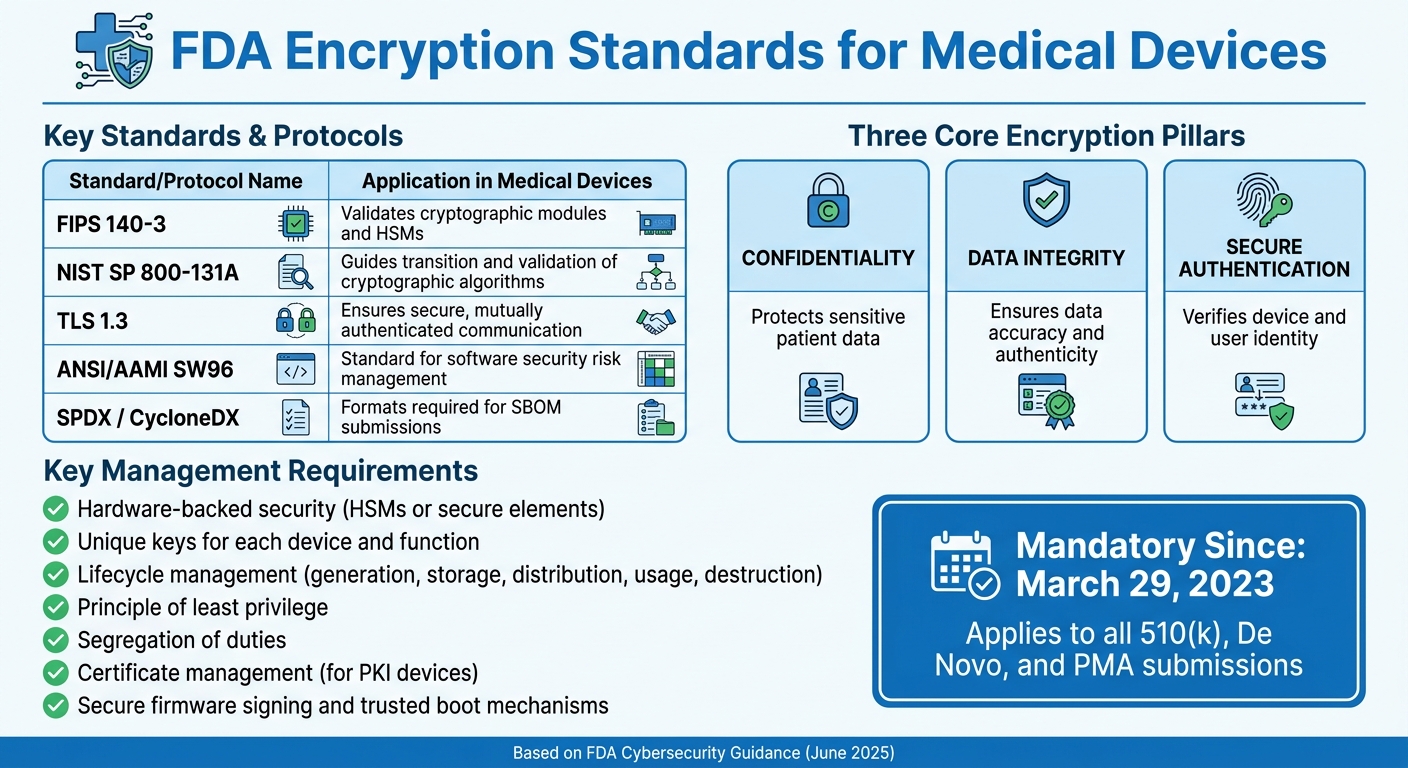
The FDA now requires medical devices to meet strict encryption standards to protect patient data and ensure device security. Since March 29, 2023, cybersecurity compliance, including encryption, is mandatory for all premarket submissions. Devices must follow specific guidelines for safeguarding sensitive health information during storage, transmission, and operation.
Key points include:
- Encryption must ensure confidentiality, data integrity, and secure authentication.
- Compliance with standards like FIPS 140-3 and TLS 1.3 is required.
- Manufacturers must provide a detailed cybersecurity plan, including encryption methods and key management practices.
- Devices need secure firmware signing, trusted boot mechanisms, and lifecycle key management.
The FDA emphasizes secure implementation over just algorithm selection. Manufacturers must document encryption strategies and validate their effectiveness to gain approval. These steps are critical for protecting patient safety and meeting regulatory requirements.
FDA’s New Guidance on Cybersecurity for Medical Devices
sbb-itb-535baee
FDA Encryption Requirements for Medical Devices
FDA Encryption Standards and Requirements for Medical Devices
Premarket Cybersecurity Guidance Overview
As of March 29, 2023, encryption is no longer just a recommended practice for medical devices - it’s now a legal requirement under Section 524B of the FD&C Act for all premarket submissions [3][4]. The FDA cemented this shift with its final guidance, "Cybersecurity in Medical Devices: Quality System Considerations and Content of Premarket Submissions", released on June 27, 2025, replacing the earlier version from September 2023 [3][4].
This guidance applies to devices submitted through 510(k), De Novo, and Premarket Approval (PMA) pathways that include software or network connectivity [2]. Manufacturers are now required to submit a detailed cybersecurity plan. This plan must outline how security is built into the device's architecture, including encryption methods, authentication protocols, and strategies to protect data both at rest and during transmission [2]. With these requirements, cybersecurity has moved from being a post-market consideration to a prerequisite for market entry [2].
"Manufacturers must design, develop, and maintain devices with cybersecurity in mind to ensure device safety and effectiveness." - FDA Guidance [4]
Next, let’s explore the encryption standards the FDA uses to assess cybersecurity measures.
Encryption Standards Referenced by the FDA
The FDA relies on standards from the National Institute of Standards and Technology (NIST) to evaluate encryption practices. Key standards include FIPS 140-3 and NIST SP 800-131A [1]. FIPS 140-3 focuses on validating cryptographic modules and Hardware Security Modules (HSMs), while NIST SP 800-131A provides guidance on transitioning and validating cryptographic algorithms and key lengths [1].
For secure communication, the FDA recommends using TLS 1.3, which supports mutual authentication and cryptographic identity management between devices and servers [1]. Additionally, manufacturers must align with ANSI/AAMI SW96, a recognized standard for managing software security risks in medical devices [4]. Premarket submissions must also include a Software Bill of Materials (SBOM) in machine-readable formats like SPDX or CycloneDX, enabling the identification of vulnerabilities in third-party cryptographic libraries [2].
| Standard/Protocol | Application in Medical Devices |
|---|---|
| FIPS 140-3 | Validates cryptographic modules and HSMs [1] |
| NIST SP 800-131A | Guides the transition and validation of cryptographic algorithms [1] |
| TLS 1.3 | Ensures secure, mutually authenticated communication [1] |
| ANSI/AAMI SW96 | Standard for software security risk management [4] |
| SPDX / CycloneDX | Formats required for SBOM submissions [2] |
Beyond these standards, effective key management practices are essential to protect the encryption lifecycle.
Key Management Requirements
Strong key management is a cornerstone of the FDA’s cybersecurity expectations. Manufacturers must adopt a lifecycle approach to cryptographic keys, addressing secure generation, storage, distribution, usage, and eventual destruction [5]. Submissions should include a risk-based rationale for the chosen cryptographic strategy, covering algorithm selection, key lengths, and management methods [5].
The FDA strongly supports hardware-backed security - such as HSMs or secure elements - for storing cryptographic keys [5]. Key management processes should also adhere to the "principle of least privilege" and ensure "segregation of duties" [5]. For devices that use Public Key Infrastructure (PKI), the FDA closely examines certificate management practices, including the choice of Certificate Authorities (CAs) and procedures for certificate revocation and renewal [5]. To minimize risks, manufacturers are encouraged to use unique keys for each device and function [1].
"The FDA's position on cryptography in medical devices is not about mandating specific algorithms but rather about ensuring their secure and appropriate implementation within a robust cybersecurity framework." - Medcrypt [5]
Devices must also incorporate secure firmware signing and trusted boot mechanisms, ensuring only authorized code runs on the device [1]. Premarket submissions must demonstrate that secure design and update processes are integrated into the system, including rollback capabilities and coordinated updates across embedded, mobile, and cloud platforms [4].
How to Implement FDA-Compliant Encryption
This section outlines actionable steps to meet the FDA's encryption requirements, focusing on selecting appropriate algorithms, integrating encryption into device design, and validating its implementation.
Choosing Approved Encryption Algorithms
While the FDA doesn't specify exact encryption algorithms, manufacturers must justify their choices through a risk-based assessment that ensures authenticity, integrity, and confidentiality of the data [1]. Algorithms validated under FIPS 140-3 and SP 800-131A are strongly recommended [1].
For symmetric encryption, AES with suitable key lengths is a reliable choice for protecting both data at rest and in transit. For asymmetric cryptography, RSA and Elliptic Curve Cryptography (ECC) are widely accepted. However, the FDA emphasizes that the quality of implementation is just as critical as the algorithm itself [5]. Devices with limited resources may rely on symmetric keys despite added complexity, but manufacturers must thoroughly document the reasoning behind this decision [5].
"The FDA's focus transcends simply selecting appropriate cryptography algorithms... The agency is intensifying scrutiny around how these algorithms are employed within the specific context of a medical device and its intended use."
– Medcrypt [5]
Use well-established, validated cryptographic libraries. For devices with long lifespans - often decades - design for cryptographic agility. This allows you to transition to stronger algorithms in the future without requiring major hardware changes, especially as quantum computing poses new security challenges [5].
Once algorithms are selected, encryption must be seamlessly integrated into the device design.
Building Encryption into Device Design
Encryption should be part of the design process from the very beginning, guided by a Secure Product Development Framework (SPDF) [1]. Medical devices often operate in resource-constrained environments with limited processing power and intermittent connectivity, so traditional IT cryptography approaches may not always apply [1].
Start by assigning unique keys to each device and function. Avoid shared credentials to ensure that a single compromised key doesn't jeopardize the entire system [1]. Use hardware-backed security solutions, such as FIPS 140-3–validated Hardware Security Modules (HSMs) or secure elements, for secure key storage and generation [1][5]. These tools help establish a strong "Root of Trust."
For secure communication, implement TLS 1.3 with mutual authentication to ensure trusted connections between devices and servers [1]. Avoid self-signed certificates in production environments. Instead, rely on trusted Certificate Authorities (CAs) to provide verifiable trust anchors and manageable certificate revocation processes [5]. Additionally, include secure firmware signing, trusted boot mechanisms, and anti-replay protections to ensure that only authorized code runs on the device [1].
Plan for the entire cryptographic lifecycle during the design phase. This includes key generation, distribution, rotation, revocation, and destruction [1]. Automating these processes can reduce the risk of human error and streamline operations [1].
Once encryption is built into the design, it’s crucial to validate its effectiveness through rigorous testing.
Testing and Validating Encryption
To meet FDA guidelines, encryption must be tested across all operational scenarios. Use tools like code analysis, vulnerability scanning, and penetration testing to confirm that your encryption supports authenticity, integrity, and confidentiality [5].
Simulate real-world scenarios during testing, such as intermittent network connectivity, power disruptions during encryption processes, and attempts to load unauthorized firmware. Verify that secure boot mechanisms block tampering and that encryption remains effective under all conditions. For devices using public key infrastructure (PKI), ensure the certificate management workflow - including provisioning, renewal, and revocation - is robust and error-free [5].
Document every step of the process. Your FDA submission should include:
- Evidence that encryption protects data at rest and in transit.
- Test results confirming compliance with FDA requirements.
- Validation of key management processes adhering to principles like least privilege and segregation of duties [5].
If needed, consult experts familiar with FDA expectations and the specific challenges of medical devices. For instance, Medcrypt has a strong track record of helping manufacturers meet FDA cybersecurity documentation standards [6]. Proper implementation and thorough documentation can greatly improve the chances of regulatory approval.
Common Encryption Compliance Challenges and Solutions
Meeting FDA encryption standards can be a complex process. Manufacturers often grapple with hurdles like limited resources or outdated systems. Tackling these issues effectively is key to avoiding prolonged regulatory setbacks.
Maintaining Security Without Compromising Performance
FDA requirements go hand-in-hand with performance challenges, especially for medical devices. These devices often operate under tight constraints, such as limited processing power, finite battery life, and real-time performance needs. As Medcrypt highlights, "Using 'off-the-shelf' IT cryptography is often insufficient - devices require domain-specific implementation." This means manufacturers need encryption solutions tailored to their device's specific limitations. For instance, lightweight symmetric algorithms like AES can secure data effectively without straining the device's limited hardware capabilities.
Updating Legacy Devices to Meet Encryption Standards
Many legacy medical devices predate the FDA's September 2023 Premarket Cybersecurity Guidance. These older systems often rely on outdated practices, such as shared keys, weak credential storage, and inadequate mechanisms for key rotation or revocation. To bring these devices up to standard, manufacturers can replace shared keys with unique credentials, isolating potential breaches. For devices with sporadic connectivity, robust local key management systems that function independently of constant cloud access are essential. In cases where hardware limitations prevent modern encryption upgrades, manufacturers may need to consider hardware replacements or plan for end-of-life transitions instead of relying on insecure software patches. These updates should fit into a broader lifecycle strategy for managing encryption.
Managing Encryption Throughout the Device Lifecycle
Encryption isn’t a one-and-done task - it requires ongoing management over the device's entire lifespan. Automated certificate management can help avoid the risks associated with manual provisioning and renewal processes. Additionally, manufacturers need to prepare for cryptographic transitions as algorithms become outdated or as new threats, like quantum computing, emerge. This means designing systems that can adopt stronger encryption standards without requiring major hardware changes. Aligning encryption measures with the FDA's pillars of confidentiality, integrity, and authenticity ensures that every security control has a clear purpose and can be validated during FDA reviews.
"Cryptography isn't just about encryption - it's about establishing trust."
Conclusion
Why Encryption Matters for Medical Device Security
The FDA describes cryptography as a "cornerstone" of medical device security [1]. Encryption safeguards sensitive patient information while ensuring that medical devices maintain the critical cybersecurity principles of authenticity, integrity, and confidentiality. It also strengthens trust by enabling secure firmware signing, trusted boot mechanisms, and mutual authentication - fortifying security at every layer. Without effective encryption, devices become vulnerable to breaches, potentially jeopardizing patient safety and leading to regulatory repercussions.
Steps to Achieve FDA Encryption Compliance
Given its essential role, achieving encryption compliance involves a structured approach. Start by generating unique cryptographic keys for each device and function, avoiding shared credentials entirely. Establish comprehensive key management practices, including regular rotation, revocation, and renewal. Use FIPS 140-3–validated hardware security modules (HSMs) and ensure encryption algorithms align with NIST standards like SP 800-131A for regulatory alignment. Steer clear of generic IT cryptography tools that may not address the specific challenges of medical devices. Additionally, map cryptographic functions to the FDA's SPDF framework to clearly demonstrate compliance.
Using Risk Management Platforms for Compliance
Risk management platforms can simplify these processes. For example, Censinet RiskOps™ provides healthcare organizations and medical device manufacturers with tools to manage cybersecurity risks tied to medical devices, patient data, and protected health information (PHI). The platform facilitates collaborative risk assessments and benchmarking, making it easier to document and validate encryption practices throughout the device lifecycle. By consolidating risk management efforts, manufacturers can expedite their FDA submission readiness and adapt to evolving cryptographic standards and emerging threats.
FAQs
Which devices must follow the FDA’s encryption rules?
Devices equipped with network connectivity or software components must meet the FDA's encryption and cybersecurity standards. These regulations are designed to safeguard patient information and ensure secure, reliable device performance throughout their entire lifecycle.
How do I prove encryption compliance in a premarket submission?
To show encryption compliance in a premarket submission, you’ll need to include documentation that proves encryption is part of the device’s design and lifecycle. This means submitting a cybersecurity management plan, along with detailed threat modeling and risk assessments that specifically address the encryption methods being used.
You should also provide evidence of secure cryptographic implementations. This can include things like module validation or certifications that demonstrate the robustness of your encryption. Additionally, explain how encryption is being used to safeguard communication, data storage, and firmware updates within the device.
Make sure all submitted materials meet the FDA’s expectations for encryption compliance to avoid delays or issues in the approval process.
What key management mistakes cause FDA review delays?
Several common mistakes can slow down FDA reviews, especially when it comes to cybersecurity and risk management. These include:
- Inadequate cybersecurity planning: Without a clear strategy for addressing potential cyber threats, devices may fail to meet FDA expectations.
- Insufficient threat modeling: Overlooking potential vulnerabilities or failing to properly assess security risks can raise red flags during the review.
- Incomplete risk assessments: A lack of detailed evaluations of risks and their mitigation strategies can result in delays.
- Poor documentation of security measures: Failing to clearly document implemented security protocols makes it harder to demonstrate compliance.
- Failure to show secure design and vulnerability management: The FDA expects evidence of secure design principles and ongoing efforts to manage vulnerabilities throughout the device's lifecycle.
To avoid these pitfalls, focus on detailed planning and thorough documentation at every stage. This not only helps meet FDA standards but also keeps the review process moving smoothly.


